Click Studios, the Australian software company behind the Passwordstate password management application, has notified customers to reset their passwords following a software supply chain attack. The Adelaide-based firm said a bad actor used sophisticated techniques to compromise the software's update mechanism and used it to drop malware on user computers. The breach is said to … [Read more...] about Passwordstate Password Manager Update Hijacked to Install Backdoor on Thousands of PCs
New QNAP NAS Flaws Exploited In Recent Ransomware Attacks
A new ransomware strain called "Qlocker" is targeting QNAP network attached storage (NAS) devices as part of an ongoing campaign and encrypting files in password-protected 7zip archives. First reports of the infections emerged on April 20, with the adversaries behind the operations demanding a bitcoin payment (0.01 bitcoins or about $500.57) to receive the decryption key. In … [Read more...] about New QNAP NAS Flaws Exploited In Recent Ransomware Attacks
Top 5 most dangerous ransomware in 2021
Over the past five years, ransomware has evolved from being a threat to individual computers to posing a serious danger to corporate networks. Cybercriminals have stopped simply trying to infect as many computers as possible and are now targeting big victims instead. Attacks on commercial organizations and government agencies require careful planning but can potentially lead to … [Read more...] about Top 5 most dangerous ransomware in 2021
Researchers Find Additional Infrastructure Used By SolarWinds Hackers
The sprawling SolarWinds cyberattack which came to light last December was known for its sophistication in the breadth of tactics used to infiltrate and persist in the target infrastructure, so much so that Microsoft went on to call the threat actor behind the campaign "skillful and methodic operators who follow operations security (OpSec) best practices to minimize traces, … [Read more...] about Researchers Find Additional Infrastructure Used By SolarWinds Hackers
The Need for Continuous and Dynamic Threat Modeling
This blog is co-authored by Mohammad Iqbal and is part four of a four-part series about DevSecOps. The trend towards accelerated application development, and regular updates to an architecture through an agile methodology, reduces the efficacy and effectiveness of point-in-time threat modeling. This recognition led us to explore and strategize ways to continuously, and … [Read more...] about The Need for Continuous and Dynamic Threat Modeling
Improve Your Cyber Security Posture by Combining State of the Art Security Tools
Today there are plenty of cybersecurity tools on the market. It is now more important than ever that the tools you decide to use work well together. If they don't, you will not get the complete picture, and you won't be able to analyze the entire system from a holistic perspective. This means that you won't be able to do the right mitigations to improve your security posture. … [Read more...] about Improve Your Cyber Security Posture by Combining State of the Art Security Tools
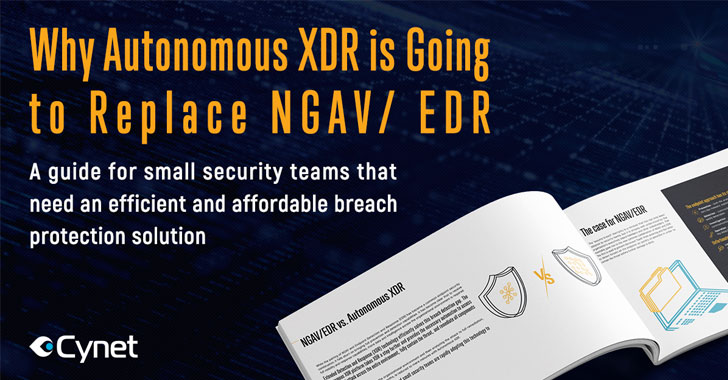
[eBook] Why Autonomous XDR Is Going to Replace NGAV/EDR
For most organizations today, endpoint protection is the primary security concern. This is not unreasonable – endpoints tend to be the weakest points in an environment – but it also misses the forest for the trees. As threat surfaces expand, security professionals are harder pressed to detect threats that target other parts of an environment and can easily miss a real … [Read more...] about [eBook] Why Autonomous XDR Is Going to Replace NGAV/EDR
Buyers of mining equipment scammed for bitcoins
Rising cryptocurrency prices have led to an increase in demand for mining equipment, but COVID-19 restrictions have led to a drop in supply. As a result, the world is witnessing another shortage of powerful video cards and cryptomining equipment, with months-long wait times for new deliveries. Cybercriminals, as always, are looking to capitalize on the crisis. For example, … [Read more...] about Buyers of mining equipment scammed for bitcoins
11 Resources to Help You Get Started in the Cybersecurity Industry
The cybersecurity industry is hiring. In November 2018, The New York Times reported that a total of 3.5 million cybersecurity jobs would be available but go unfilled by 2021. This employment gap increased in the year that followed. (ISC)2 estimated at the end of 2019 that it would take 4.07 million trained professionals to fill all available cybersecurity positions—a 62% … [Read more...] about 11 Resources to Help You Get Started in the Cybersecurity Industry
Malware That Spreads Via Xcode Projects Now Targeting Apple’s M1-based Macs
A Mac malware campaign targeting Xcode developers has been retooled to add support for Apple's new M1 chips and expand its features to steal confidential information from cryptocurrency apps. XCSSET came into the spotlight in August 2020 after it was found to spread via modified Xcode IDE projects, which, upon the building, were configured to execute the payload. The malware … [Read more...] about Malware That Spreads Via Xcode Projects Now Targeting Apple’s M1-based Macs