Security researchers have uncovered nine vulnerabilities affecting four TCP/IP stacks impacting more than 100 million consumer and enterprise devices that could be exploited by an attacker to take control of a vulnerable system. Dubbed "NAME:WRECK" by Forescout and JSOF, the flaws are the latest in series of studies undertaken as part of an initiative called Project Memoria to … [Read more...] about New NAME:WRECK Vulnerabilities Impact Nearly 100 Million IoT Devices
Screenshot cryptoscam in Lightshot | Kaspersky official blog
Cryptocurrency scams seem to be gaining momentum by the day. Hard on the heels of scammers tricking Discord users by offering nonexistent coins on fake exchanges, inventing stories about lucky winners on fake news sites, and simulating helicopter money, a new scheme is exploiting Lightshot’s screen-sharing tool to get money from overly curious cryptoinvestors. Convenient … [Read more...] about Screenshot cryptoscam in Lightshot | Kaspersky official blog
Securing AWS EKS Environments – Cisco Blogs
So, your organization’s simplifying Kubernetes management with AWS’s Elastic Kubernetes Service (EKS). Now, how are you going to secure that cluster? Whether your role is on the application team, or in DevOps or SecOps, you might be thinking: We chose EKS because agility is important to us. Similarly, we need manageable and efficient security, so we can stay focused on what … [Read more...] about Securing AWS EKS Environments – Cisco Blogs
What Does It Take To Be a Cybersecurity Researcher?
Behind the strategies and solutions needed to counter today's cyber threats are—dedicated cybersecurity researchers. They spend their lives dissecting code and analyzing incident reports to discover how to stop the bad guys. But what drives these specialists? To understand the motivations for why these cybersecurity pros do what they do, we decided to talk with cybersecurity … [Read more...] about What Does It Take To Be a Cybersecurity Researcher?
Hackers Tampered With APKPure Store to Distribute Malware Apps
APKPure, one of the largest alternative app stores outside of the Google Play Store, was infected with malware this week, allowing threat actors to distribute Trojans to Android devices. In an incident that's similar to that of German telecommunications equipment manufacturer Gigaset, the APKPure client version 3.17.18 is said to have been tampered with in an attempt to trick … [Read more...] about Hackers Tampered With APKPure Store to Distribute Malware Apps
APKPure is not safe, distributes Trojans
We always recommend downloading apps from official stores only, to reduce the likelihood of installing malware. However, unofficial stores not only host malicious apps, but they might not be safe at all. Following a recent investigation, we are sorry to report that APKPure, a popular alternative source of Android apps, was Trojanized and has been distributing other … [Read more...] about APKPure is not safe, distributes Trojans
Alert — There’s A New Malware Out There Snatching Users’ Passwords
A previously undocumented malware downloader has been spotted in the wild in phishing attacks to deploy credential stealers and other malicious payloads. Dubbed "Saint Bot," the malware is said to have first appeared on the scene in January 2021, with indications that it's under active development. "Saint Bot is a downloader that appeared quite recently, and slowly is getting … [Read more...] about Alert — There’s A New Malware Out There Snatching Users’ Passwords
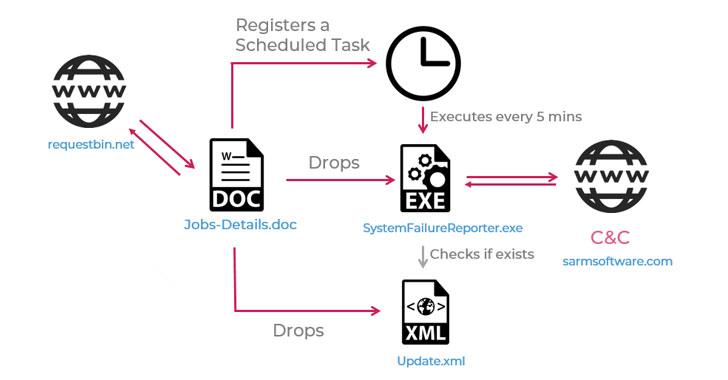
Researchers uncover a new Iranian malware used in recent cyberattacks
An Iranian threat actor has unleashed a new cyberespionage campaign against a possible Lebanese target with a backdoor capable of exfiltrating sensitive information from compromised systems. Cybersecurity firm Check Point attributed the operation to APT34, citing similarities with previous techniques used by the threat actor as well as based on its pattern of victimology. APT34 … [Read more...] about Researchers uncover a new Iranian malware used in recent cyberattacks
The Rise of Telemetry Architecture
There was a time not so long ago when you were at a party and another party goer asked the question “Oh, and what do you do for a living?” Odds are, their answer might have simply been something like “I’m an architect” and from that you could infer that they designed and authored blueprints for construction related to houses and buildings. But these days, you can be a network … [Read more...] about The Rise of Telemetry Architecture
Ransomware: From blockers to cryptors and beyond
If you follow information security, you have probably heard a lot about ransomware in recent years. You may even have had the misfortune of being on the receiving end of an attack. It is perhaps no exaggeration to describe ransomware as the most dangerous malware of our time. But did you know that such malicious programs have been around for more than 30 years, and that … [Read more...] about Ransomware: From blockers to cryptors and beyond