Jan 24, 2024NewsroomCloud Security / Kubernetes Cybersecurity researchers have discovered a loophole impacting Google Kubernetes Engine (GKE) that could be potentially exploited by threat actors with a Google account to take control of a Kubernetes cluster. The critical shortcoming has been codenamed Sys:All by cloud security firm Orca. As many as 250,000 active GKE clusters … [Read more...] about Google Kubernetes Misconfig Lets Any Gmail Account Control Your Clusters
Control
Hackers Abusing GitHub to Evade Detection and Control Compromised Hosts
Dec 19, 2023The Hacker NewsSoftware Security / Threat intelligence Threat actors are increasingly making use of GitHub for malicious purposes through novel methods, including abusing secret Gists and issuing malicious commands via git commit messages. "Malware authors occasionally place their samples in services like Dropbox, Google Drive, OneDrive, and Discord to host second … [Read more...] about Hackers Abusing GitHub to Evade Detection and Control Compromised Hosts
Take control of your Elastic Cloud spend with data-driven insights
As we continue to expand our product offerings, new products, and services will be integrated into the usage page. The latest addition to this offering is Synthetic Monitoring. This feature offers insights into the utilization and expenses associated with synthetics products, making it easier to manage and optimize your overall spending.We encourage you to explore the enriched … [Read more...] about Take control of your Elastic Cloud spend with data-driven insights
Industrial control systems security with Elastic Security and Zeek
Keeping track of all ICS asset history and accurate status in a global inventory is critical not only for purposes like maintenance, cost management, and environment optimization but also for the system's security. Well-implemented and maintained inventories are key to ICS security programs, since you can’t protect what you don’t know about. Knowing what is on the ICS network, … [Read more...] about Industrial control systems security with Elastic Security and Zeek
CISA Warns of Flaws in Siemens, GE Digital, and Contec Industrial Control Systems
Jan 18, 2023Ravie LakshmananICS/SCADA Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has published four Industrial Control Systems (ICS) advisories, calling out several security flaws affecting products from Siemens, GE Digital, and Contec. The most critical of the issues have been identified in Siemens SINEC INS that could lead to remote code … [Read more...] about CISA Warns of Flaws in Siemens, GE Digital, and Contec Industrial Control Systems
Crypto Miners Using Tox P2P Messenger as Command and Control Server
Threat actors have begun to use the Tox peer-to-peer instant messaging service as a command-and-control method, marking a shift from its earlier role as a contact method for ransomware negotiations. The findings from Uptycs, which analyzed an Executable and Linkable Format (ELF) artifact ("72client") that functions as a bot and can run scripts on the compromised host using the … [Read more...] about Crypto Miners Using Tox P2P Messenger as Command and Control Server
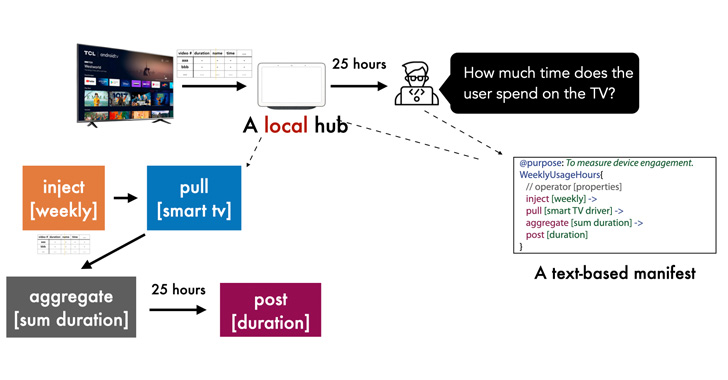
New Privacy Framework for IoT Devices Gives Users Control Over Data Sharing
A newly designed privacy-sensitive architecture aims to enable developers to create smart home apps in a manner that addresses data sharing concerns and puts users in control over their personal information. Dubbed Peekaboo by researchers from Carnegie Mellon University, the system "leverages an in-home hub to pre-process and minimize outgoing data in a structured and … [Read more...] about New Privacy Framework for IoT Devices Gives Users Control Over Data Sharing
JekyllBot:5 Flaws Let Attackers Take Control of Aethon TUG Hospital Robots
As many as five security vulnerabilities have been addressed in Aethon Tug hospital robots that could enable remote attackers to seize control of the devices and interfere with the timely distribution of medication and lab samples. "Successful exploitation of these vulnerabilities could cause a denial-of-service condition, allow full control of robot functions, or expose … [Read more...] about JekyllBot:5 Flaws Let Attackers Take Control of Aethon TUG Hospital Robots
Taking Full Control of your Telemetry with the Intelligent Telemetry Plane
Earlier this year, we introduced the Cisco Telemetry Broker (CTB) and showed customers how it can free their telemetry from proprietary protocols and allow them to use the tools and solutions they already have in place to coexist seamlessly. Today, we would like to introduce you all to the notion of the Intelligent Telemetry Plane. Products in the market today like the UDP … [Read more...] about Taking Full Control of your Telemetry with the Intelligent Telemetry Plane
Building Consumer Confidence Through Transparency and Control
Protecting privacy continues to be a critical issue for individuals, organizations, and governments around the world. Eighteen months into the COVID-19 pandemic, our health information and vaccination status are needed more than ever to understand the virus, control the spread, and enable safer environments for work, learning, recreation, and other activities. Nonetheless, … [Read more...] about Building Consumer Confidence Through Transparency and Control