May 15, 2023Ravie LakshmananCyber Threat / Malware Government, aviation, education, and telecom sectors located in South and Southeast Asia have come under the radar of a new hacking group as part of a highly-targeted campaign that commenced in mid-2022 and continued into the first quarter of 2023. Symantec, by Broadcom Software, is tracking the activity under its … [Read more...] about Researchers Uncover Powerful Backdoor and Custom Implant in Year-Long Cyber Campaign
Custom
Introduction to custom machine learning models and maps
Introduction to custom machine learning models and mapsHow to use text-based datasets to build beautiful dashboards leveraging mapsEnglish简体中文한국어日本語FrançaisDeutschEspañolPortuguêsIn Elasticsearch 8.0, we introduced the ability to run custom machine learning models, such as the ones based on BERT (Bidirectional Encoder Representations from Transformers), to perform natural … [Read more...] about Introduction to custom machine learning models and maps
How Falcon OverWatch Detected SILENT CHOLLIMA’s Custom Tooling
CrowdStrike Falcon OverWatch™ recently released its annual threat hunting report, detailing the interactive intrusion activity observed by hunters over the course of the past year. The tactics, techniques and procedures (TTPs) an adversary uses serve as key indicators to threat hunters of who might be behind an intrusion. OverWatch threat hunters uncovered an intrusion against … [Read more...] about How Falcon OverWatch Detected SILENT CHOLLIMA’s Custom Tooling
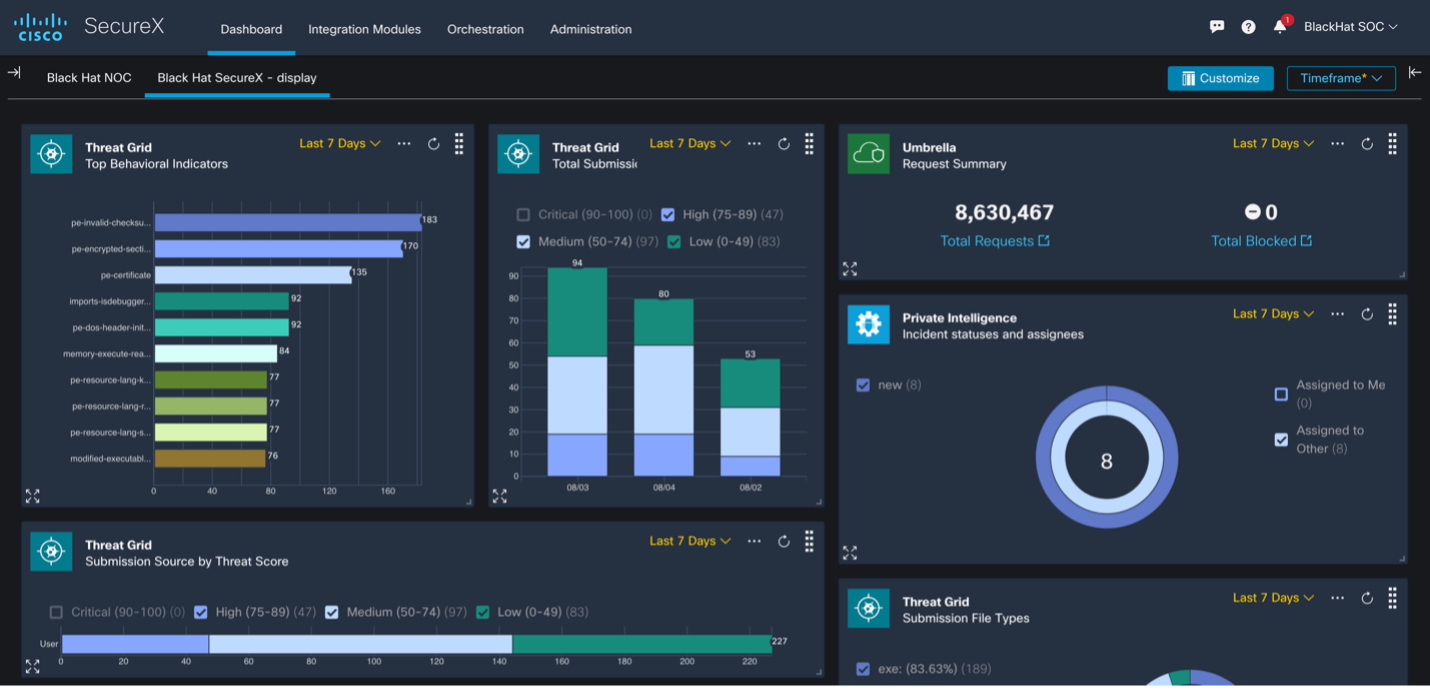
Building a Custom SecureX Orchestration Workflow for Umbrella
Improving efficiency for the Cisco team in the Black Hat USA NOC As a proud partner of the Black Hat USA NOC, Cisco deployed multiple technologies along with the other Black Hat NOC partners to build a stable and secure network for the conference. We used Cisco Secure Malware Analytics to analyze files and monitor any potential PII leaks. We also used Meraki SM to manage over … [Read more...] about Building a Custom SecureX Orchestration Workflow for Umbrella
Crafting a Custom Dictionary for Your Password Policy
Modern password policies are comprised of many different elements that contribute to its effectiveness. One of the components of an effective current password policy makes use of what is known as a custom dictionary that filters out certain words that are not allowed as passwords in the environment. Using custom dictionaries, organizations can significantly improve their … [Read more...] about Crafting a Custom Dictionary for Your Password Policy
Reducing the Attack Surface with Custom Indicators of Attack
Introduction As many organizations around the globe are settling into longer-term remote working situations for their employees, IT Hygiene should be at the forefront of preventative security protocol. Adversaries are getting increasingly savvy, taking advantage of changes in work environments. Since IT hygiene requires even more oversight than before, how can security teams … [Read more...] about Reducing the Attack Surface with Custom Indicators of Attack
How to Use Custom Filters in Falcon Spotlight
Introduction This article and video will provide an overview of the power of custom filters in Falcon Spotlight. Spotlight provides customers with realtime data about the vulnerabilities in the environment. With custom filters, organizations can quickly sort that data to focus on critical assets, vulnerabilities and remediations. Those filters can then be saved for repeat use … [Read more...] about How to Use Custom Filters in Falcon Spotlight
Reducing the Attack Surface with Custom Indicators of Attack
Introduction The evolving nature of malicious activity is keeping security teams on their toes. Adversaries may start with commodity malware but quickly shift tactics as they encounter resistance or zero-in on their specific target. As tactics get more targeted and tailored, detection and protection can get more complicated. Can security teams easily customize protection rules … [Read more...] about Reducing the Attack Surface with Custom Indicators of Attack