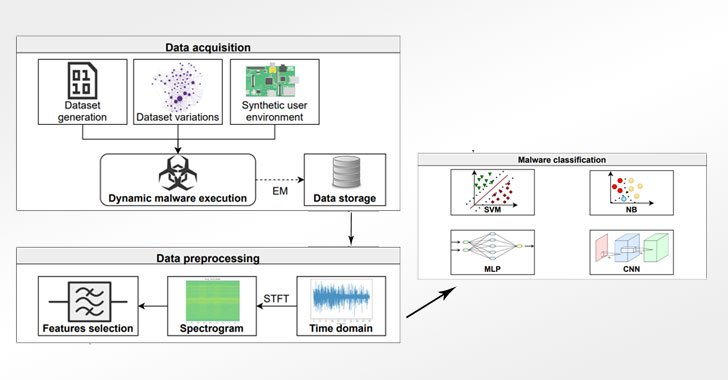
Cybersecurity researchers have proposed a novel approach that leverages electromagnetic field emanations from the Internet of Things (IoT) devices as a side-channel to glean precise knowledge about the different kinds of malware targeting the embedded systems, even in scenarios where obfuscation techniques have been applied to hinder analysis. With the rapid adoption of IoT … [Read more...] about Detecting Evasive Malware on IoT Devices Using Electromagnetic Emanations
cyber attacks
New iLOBleed Rootkit Targeting HP Enterprise Servers with Data Wiping Attacks
A previously unknown rootkit has been found setting its sights on Hewlett-Packard Enterprise's Integrated Lights-Out (iLO) server management technology to carry out in-the-wild attacks that tamper with the firmware modules and completely wipe data off the infected systems. The discovery, which is the first instance of real-world malware in iLO firmware, was documented by … [Read more...] about New iLOBleed Rootkit Targeting HP Enterprise Servers with Data Wiping Attacks
Chinese APT Hackers Used Log4Shell Exploit to Target Academic Institution
A never-before-seen China-based targeted intrusion adversary dubbed Aquatic Panda has been observed leveraging critical flaws in the Apache Log4j logging library as an access vector to perform various post-exploitation operations, including reconnaissance and credential harvesting on targeted systems. Cybersecurity firm CrowdStrike said the infiltration, which was ultimately … [Read more...] about Chinese APT Hackers Used Log4Shell Exploit to Target Academic Institution
Ongoing Autom Cryptomining Malware Attacks Using Upgraded Evasion Tactics
An ongoing crypto mining campaign has upgraded its arsenal while adding new defense evasion tactics that enable the threat actors to conceal the intrusions and fly under the radar, new research published today has revealed. Since first detected in 2019, a total of 84 attacks against its honeypot servers have been recorded to date, four of which transpired in 2021, according to … [Read more...] about Ongoing Autom Cryptomining Malware Attacks Using Upgraded Evasion Tactics
New Apache Log4j Update Released to Patch Newly Discovered Vulnerability
The Apache Software Foundation (ASF) on Tuesday rolled out fresh patches to contain an arbitrary code execution flaw in Log4j that could be abused by threat actors to run malicious code on affected systems, making it the fifth security shortcoming to be discovered in the tool in the span of a month. Tracked as CVE-2021-44832, the vulnerability is rated 6.6 in severity on a … [Read more...] about New Apache Log4j Update Released to Patch Newly Discovered Vulnerability
CISA, FBI and NSA Publish Joint Advisory and Scanner for Log4j Vulnerabilities
Cybersecurity agencies from Australia, Canada, New Zealand, the U.K., and the U.S. on Wednesday released a joint advisory in response to widespread exploitation of multiple vulnerabilities in Apache's Log4j software library by nefarious adversaries. "These vulnerabilities, especially Log4Shell, are severe," the intelligence agencies said in the new guidance. "Sophisticated … [Read more...] about CISA, FBI and NSA Publish Joint Advisory and Scanner for Log4j Vulnerabilities
Experts Detail Logging Tool of DanderSpritz Framework Used by Equation Group Hackers
Cybersecurity researchers have offered a detailed glimpse into a system called DoubleFeature that's dedicated to logging the different stages of post-exploitation stemming from the deployment of DanderSpritz, a full-featured malware framework used by the Equation Group. DanderSpritz came to light on April 14, 2017, when a hacking group known as the Shadow Brokers leaked the … [Read more...] about Experts Detail Logging Tool of DanderSpritz Framework Used by Equation Group Hackers
Take Your Career to the Next Level
Cybercrime is increasing exponentially and presents devastating risks for most organizations. According to Cybercrime Magazine, global cybercrime damage is predicted to hit $10.5 trillion annually as of 2025. One of the more recent and increasingly popular forms of tackling such issues by identifying is ethical hacking. This method identifies potential security vulnerabilities … [Read more...] about Take Your Career to the Next Level
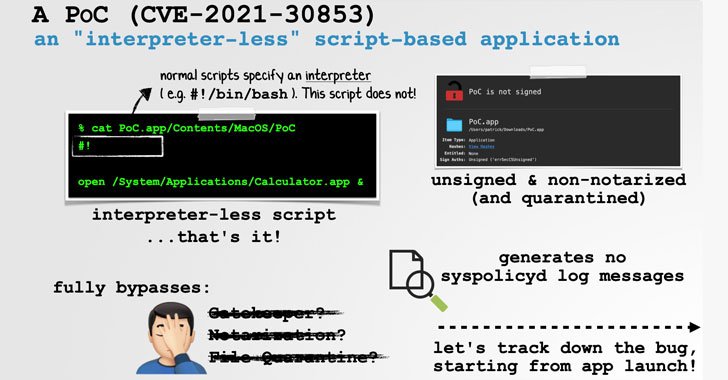
Expert Details macOS Bug That Could Let Malware Bypass Gatekeeper Security
Apple recently fixed a security vulnerability in the macOS operating system that could be potentially exploited by a threat actor to "trivially and reliably" bypass a "myriad of foundational macOS security mechanisms" and run arbitrary code. Security researcher Patrick Wardle detailed the discovery in a series of tweets on Thursday. Tracked as CVE-2021-30853 (CVSS score: 5.5), … [Read more...] about Expert Details macOS Bug That Could Let Malware Bypass Gatekeeper Security
New Ransomware Variants Flourish Amid Law Enforcement Actions
Ransomware groups continue to evolve their tactics and techniques to deploy file-encrypting malware on compromised systems, notwithstanding law enforcement's disruptive actions against the cybercrime gangs to prevent them from victimizing additional companies. "Be it due to law enforcement, infighting amongst groups or people abandoning variants altogether, the RaaS … [Read more...] about New Ransomware Variants Flourish Amid Law Enforcement Actions