A sophisticated phishing-as-a-service (PhaaS) platform called Darcula has set its sights on organizations in over 100 countries by leveraging a massive network of more than 20,000 counterfeit domains to help cyber criminals launch attacks at scale. "Using iMessage and RCS rather than SMS to send text messages has the side effect of bypassing SMS firewalls, which is being used … [Read more...] about Darcula Phishing Network Leveraging RCS and iMessage to Evade Detection
Evade
Hackers Abusing GitHub to Evade Detection and Control Compromised Hosts
Dec 19, 2023The Hacker NewsSoftware Security / Threat intelligence Threat actors are increasingly making use of GitHub for malicious purposes through novel methods, including abusing secret Gists and issuing malicious commands via git commit messages. "Malware authors occasionally place their samples in services like Dropbox, Google Drive, OneDrive, and Discord to host second … [Read more...] about Hackers Abusing GitHub to Evade Detection and Control Compromised Hosts
ShellBot Uses Hex IPs to Evade Detection in Attacks on Linux SSH Servers
Oct 12, 2023Newsroom The threat actors behind ShellBot are leveraging IP addresses transformed into its hexadecimal notation to infiltrate poorly managed Linux SSH servers and deploy the DDoS malware. "The overall flow remains the same, but the download URL used by the threat actor to install ShellBot has changed from a regular IP address to a hexadecimal value," the AhnLab … [Read more...] about ShellBot Uses Hex IPs to Evade Detection in Attacks on Linux SSH Servers
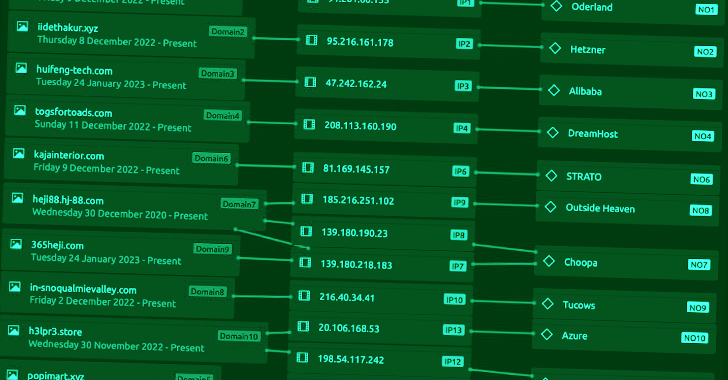
FormBook Malware Spreads via Malvertising Using MalVirt Loader to Evade Detection
Feb 06, 2023Ravie LakshmananMalvertising / Data Safety An ongoing malvertising campaign is being used to distribute virtualized .NET loaders that are designed to deploy the FormBook information-stealing malware. "The loaders, dubbed MalVirt, use obfuscated virtualization for anti-analysis and evasion along with the Windows Process Explorer driver for terminating processes," … [Read more...] about FormBook Malware Spreads via Malvertising Using MalVirt Loader to Evade Detection
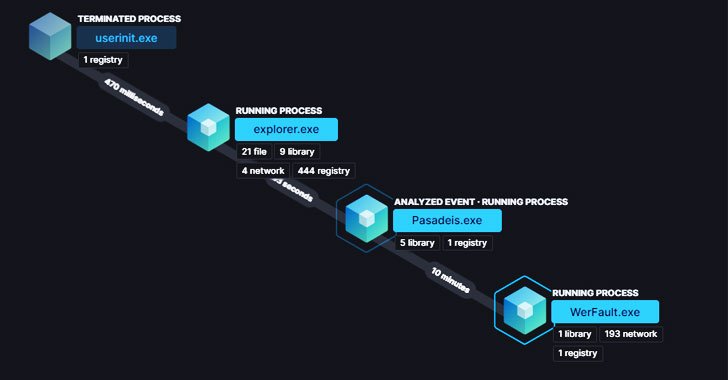
New BLISTER Malware Using Code Signing Certificates to Evade Detection
Cybersecurity researchers have disclosed details of an evasive malware campaign that makes use of valid code signing certificates to sneak past security defenses and stay under the radar with the goal of deploying Cobalt Strike and BitRAT payloads on compromised systems. The binary, a loader, has been dubbed "Blister" by researchers from Elastic Security, with the malware … [Read more...] about New BLISTER Malware Using Code Signing Certificates to Evade Detection
New Malware Targets Windows Subsystem for Linux to Evade Detection
A number of malicious samples have been created for the Windows Subsystem for Linux (WSL) with the goal of compromising Windows machines, highlighting a sneaky method that allows the operators to stay under the radar and thwart detection by popular anti-malware engines. The "distinct tradecraft" marks the first instance where a threat actor has been found abusing WSL to install … [Read more...] about New Malware Targets Windows Subsystem for Linux to Evade Detection
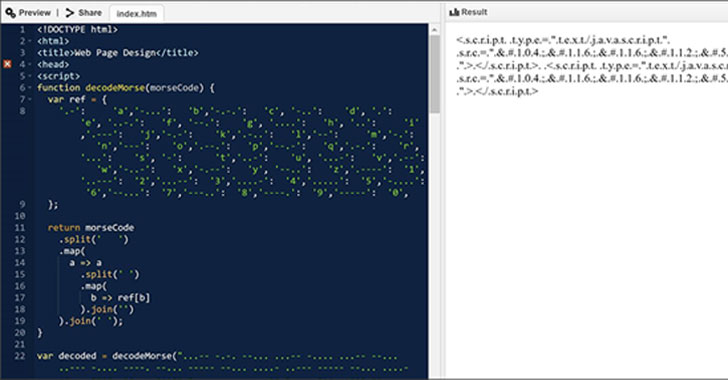
Hackers Spotted Using Morse Code in Phishing Attacks to Evade Detection
Microsoft has disclosed details of an evasive year-long social engineering campaign wherein the operators kept changing their obfuscation and encryption mechanisms every 37 days on average, including relying on Morse code, in an attempt to cover their tracks and surreptitiously harvest user credentials. The phishing attacks take the form of invoice-themed lures mimicking … [Read more...] about Hackers Spotted Using Morse Code in Phishing Attacks to Evade Detection
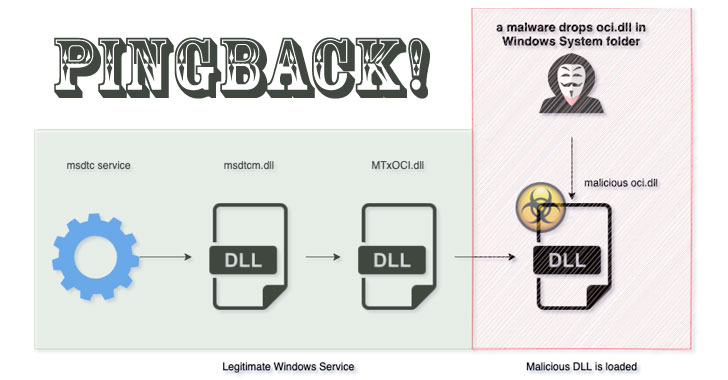
New Pingback Malware Using ICMP Tunneling to Evade C&C Detection
Researchers on Tuesday disclosed a novel malware that uses a variety of tricks to stay under the radar and evade detection, while stealthily capable of executing arbitrary commands on infected systems. Called 'Pingback,' the Windows malware leverages Internet Control Message Protocol (ICMP) tunneling for covert bot communications, allowing the adversary to utilize ICMP packets … [Read more...] about New Pingback Malware Using ICMP Tunneling to Evade C&C Detection
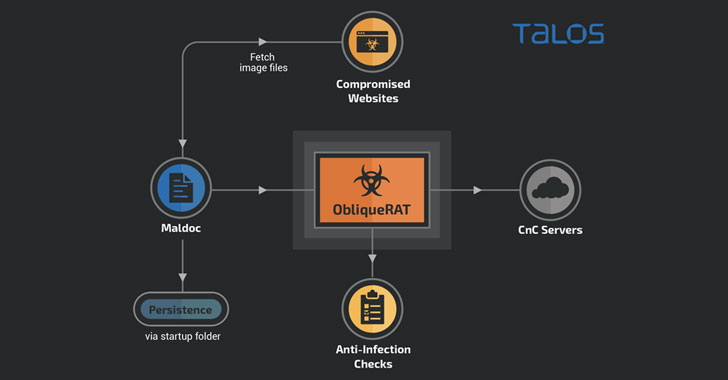
Hackers Now Hiding ObliqueRAT Payload in Images to Evade Detection
Cybercriminals are now deploying remote access Trojans (RATs) under the guise of seemingly innocuous images hosted on infected websites, once again highlighting how threat actors quickly change tactics when their attack methods are discovered and exposed publicly. New research released by Cisco Talos reveals a new malware campaign targeting organizations in South Asia that … [Read more...] about Hackers Now Hiding ObliqueRAT Payload in Images to Evade Detection