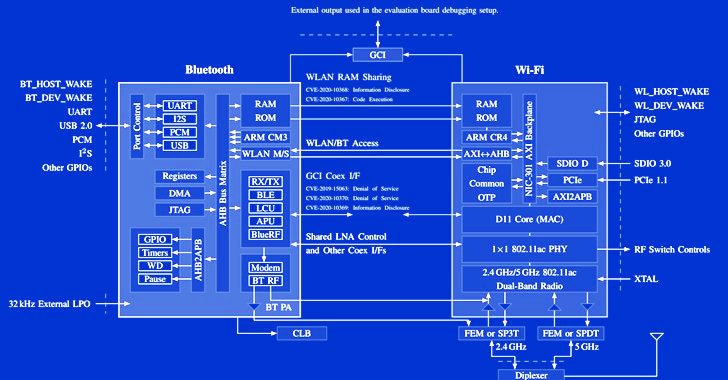
Cybersecurity researchers have demonstrated a new attack technique that makes it possible to leverage a device's Bluetooth component to directly extract network passwords and manipulate traffic on a Wi-Fi chip. The novel attacks work against the so-called "combo chips," which are specialized chips that are equipped to handle different types of radio wave-based wireless … [Read more...] about Researchers Uncover New Coexistence Attacks On Wi-Fi and Bluetooth Chips
information security
Facebook to Pay Hackers for Reporting Data Scraping Bugs and Scraped Datasets
Meta Platforms, the company formerly known as Facebook, has announced that it's expanding its bug bounty program to start rewarding valid reports of scraping vulnerabilities across its platforms as well as include reports of scraping data sets that are available online. "We know that automated activity designed to scrape people's public and private data targets every website or … [Read more...] about Facebook to Pay Hackers for Reporting Data Scraping Bugs and Scraped Datasets
Hackers Exploit Log4j Vulnerability to Infect Computers with Khonsari Ransomware
Romanian cybersecurity technology company Bitdefender on Monday revealed that attempts are being made to target Windows machines with a novel ransomware family called Khonsari as well as a remote access Trojan named Orcus by exploiting the recently disclosed critical Log4j vulnerability. The attack leverages the remote code execution flaw to download an additional payload, a … [Read more...] about Hackers Exploit Log4j Vulnerability to Infect Computers with Khonsari Ransomware
Apache Log4j Vulnerability — Log4Shell — Widely Under Active Attack
Threat actors are actively weaponizing unpatched servers affected by the newly identified "Log4Shell" vulnerability in Log4j to install cryptocurrency miners, Cobalt Strike, and recruit the devices into a botnet, even as telemetry signs point to exploitation of the flaw nine days before it even came to light. Netlab, the networking security division of Chinese tech giant Qihoo … [Read more...] about Apache Log4j Vulnerability — Log4Shell — Widely Under Active Attack
Extremely Critical Log4J Vulnerability Leaves Much of the Internet at Risk
The Apache Software Foundation has released fixes to contain an actively exploited zero-day vulnerability affecting the widely-used Apache Log4j Java-based logging library that could be weaponized to execute malicious code and allow a complete takeover of vulnerable systems. Tracked as CVE-2021-44228 and by the monikers Log4Shell or LogJam, the issue concerns a case of … [Read more...] about Extremely Critical Log4J Vulnerability Leaves Much of the Internet at Risk
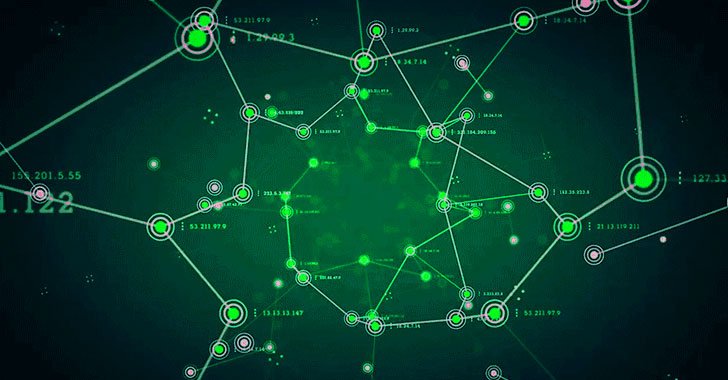
1.6 Million WordPress Sites Under Cyberattack From Over 16,000 IP Addresses
As many as 1.6 million WordPress sites have been targeted by an active large-scale attack campaign originating from 16,000 IP addresses by exploiting weaknesses in four plugins and 15 Epsilon Framework themes. WordPress security company Wordfence, which disclosed details of the attacks, said Thursday it had detected and blocked more than 13.7 million attacks aimed at the … [Read more...] about 1.6 Million WordPress Sites Under Cyberattack From Over 16,000 IP Addresses
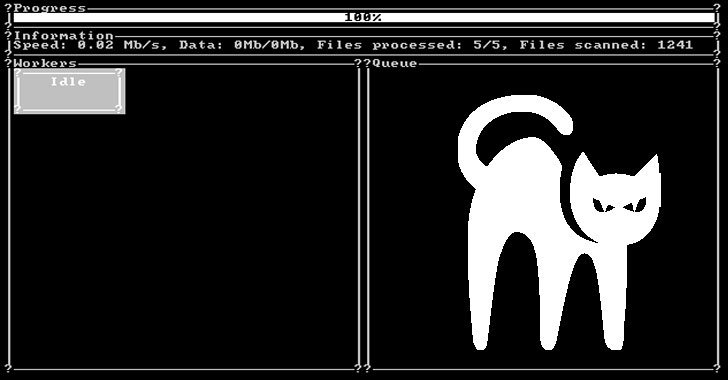
A New Rust-based Ransomware Malware Spotted in the Wild
Details have emerged about what's the first Rust-language-based ransomware strain spotted in the wild that has already amassed "some victims from different countries" since its launch last month. The ransomware, dubbed BlackCat, was disclosed by MalwareHunterTeam. "Victims can pay with Bitcoin or Monero," the researchers said in a series of tweets detailing the file-encrypting … [Read more...] about A New Rust-based Ransomware Malware Spotted in the Wild
Why Holidays Put Your Company at Risk of Cyber Attack (And How to Take Precautions)
It is a time when many are thinking of their families and loved ones, time off work, and gift-giving – the holidays. However, while many have their minds outside the realm of work during the holiday season, often, this is when attackers plan their most sinister attacks. So how can you take precautions to protect your organization during these times? Why holidays put your … [Read more...] about Why Holidays Put Your Company at Risk of Cyber Attack (And How to Take Precautions)
Google Disrupts Blockchain-based Glupteba Botnet; Sues Russian Hackers
Google on Tuesday said it took steps to disrupt the operations of a sophisticated "multi-component" botnet called Glupteba that approximately infected more than one million Windows computers across the globe and stored its command-and-control server addresses on Bitcoin's blockchain as a resilience mechanism. As part of the efforts, Google's Threat Analysis Group (TAG) said it … [Read more...] about Google Disrupts Blockchain-based Glupteba Botnet; Sues Russian Hackers
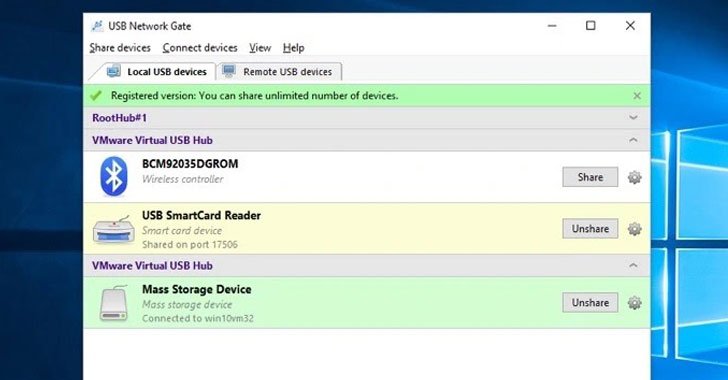
Eltima SDK Contain Multiple Vulnerabilities Affecting Several Cloud Service Provides
Cybersecurity researchers have disclosed multiple vulnerabilities in a third-party driver software developed by Eltima that have been "unwittingly inherited" by cloud desktop solutions like Amazon Workspaces, Accops, and NoMachine and could provide attackers a path to perform an array of malicious activities. "These vulnerabilities allow attackers to escalate privileges … [Read more...] about Eltima SDK Contain Multiple Vulnerabilities Affecting Several Cloud Service Provides