Hybrid Workforce is here to stay Just a few years ago when the topic of supporting offsite workers arose, some of the key conversation topics were related to purchase, logistics, deployment, maintenance and similar issues. The discussions back then were more like “special cases” vs. today’s environment where supporting workers offsite (now known as the hybrid workforce) has … [Read more...] about Secure Your Hybrid Workforce Using These SOC Best Practices
Secure
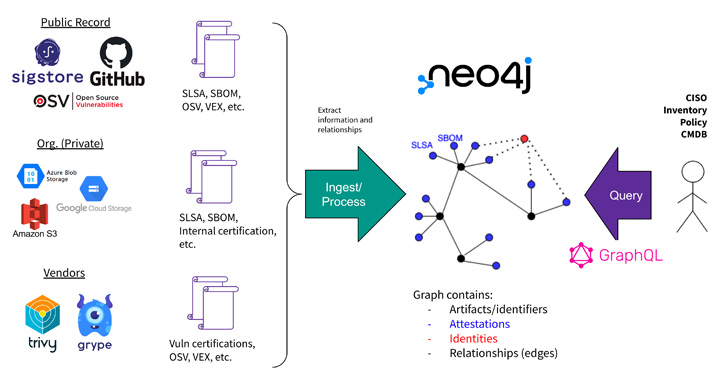
Google Launches GUAC Open Source Project to Secure Software Supply Chain
Google on Thursday announced that it's seeking contributors to a new open source initiative called Graph for Understanding Artifact Composition, also known as GUAC, as part of its ongoing efforts to beef up the software supply chain. "GUAC addresses a need created by the burgeoning efforts across the ecosystem to generate software build, security, and dependency metadata," … [Read more...] about Google Launches GUAC Open Source Project to Secure Software Supply Chain
Introducing “NEXT” by Cisco Secure
Inspiring discussions around innovative tech Technology has typically had a reputation for being exciting and inventive. Unfortunately, this hasn’t always been the case for security. But times have changed. We are now recognizing the crucial role security plays in any groundbreaking technology. Without strong defenses, even the most visionary app is likely to crash and burn. … [Read more...] about Introducing “NEXT” by Cisco Secure
Defend your organization from ransomware attacks with Cisco Secure Endpoint
Ransomware is one of the most dangerous threats organizations face today, so it’s no wonder that Cisco Talos Incident Response named it the top threat of the year in 2021. These attacks continue to grow and become more advanced, with ransomware attacks growing by 13% over 2021 and a whopping 79% over 2020 so far this year (see Figure 1 below).1 Stopping ransomware attacks … [Read more...] about Defend your organization from ransomware attacks with Cisco Secure Endpoint
Cisco Secure 5 Best Practices Security Analysts Can Use to Secure Their Hybrid Workforce.
The hybrid work environment has been around for years, albeit not common but it existed. I can recall my first job where I was able to split my time working in an office and working from my makeshift home office. This was many moons ago as I will call it… pre-COVID-19. Job seekers are certainly looking to have the flexibility of working from anywhere at any time – preferably … [Read more...] about Cisco Secure 5 Best Practices Security Analysts Can Use to Secure Their Hybrid Workforce.
Scale security on the fly in Microsoft Azure Cloud with Cisco Secure Firewall
The release of Microsoft Azure Gateway Load Balancer is great news for customers, empowering them to simply and easily add Cisco Secure Firewall capabilities to their Azure cloud infrastructure. By combining Azure Gateway Load Balancer with Cisco Secure Firewall, organizations can quickly scale their firewall presence across their Azure cloud environment, providing protection … [Read more...] about Scale security on the fly in Microsoft Azure Cloud with Cisco Secure Firewall
Announcing SOC 2 Compliance for Cisco Secure Endpoint, Cisco Secure Malware Analytics, and Cisco SecureX
With a rising number of cyberattacks targeting organizations, protecting sensitive customer information has never been more critical. The stakes are high due to the financial losses, reputational damage, legal & compliance fines, and more that often stem from mishandled data. At Cisco Secure, we recognize this and are continuously looking for ways to improve our information … [Read more...] about Announcing SOC 2 Compliance for Cisco Secure Endpoint, Cisco Secure Malware Analytics, and Cisco SecureX
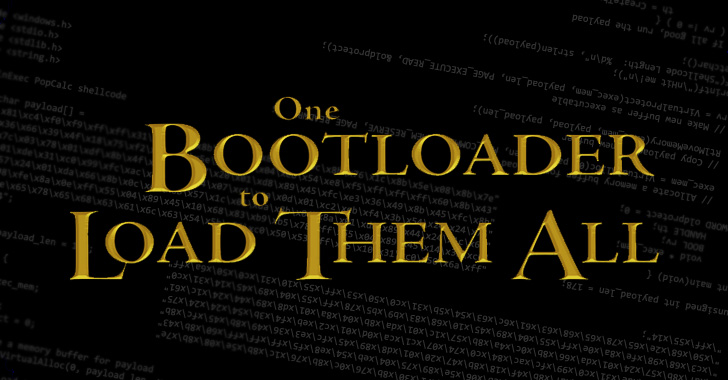
Researchers Uncover UEFI Secure Boot Bypass in 3 Microsoft Signed Boot Loaders
A security feature bypass vulnerability has been uncovered in three signed third-party Unified Extensible Firmware Interface (UEFI) boot loaders that allow bypass of the UEFI Secure Boot feature. "These vulnerabilities can be exploited by mounting the EFI System Partition and replacing the existing bootloader with the vulnerable one, or modifying a UEFI variable to load the … [Read more...] about Researchers Uncover UEFI Secure Boot Bypass in 3 Microsoft Signed Boot Loaders
More than a VPN: Announcing Cisco Secure Client (formerly AnyConnect)
We’re excited to announce Cisco Secure Client, formerly AnyConnect, as the new version of one of the most widely deployed security agents. As the unified security agent for Cisco Secure, it addresses common operational use cases applicable to Cisco Secure endpoint agents. Those who install Secure Client’s next-generation software will benefit from a shared user interface for … [Read more...] about More than a VPN: Announcing Cisco Secure Client (formerly AnyConnect)
An Easier Way to Keep Old Python Code Healthy and Secure
Python has its pros and cons, but it's nonetheless used extensively. For example, Python is frequently used in data crunching tasks even when there are more appropriate languages to choose from. Why? Well, Python is relatively easy to learn. Someone with a science background can pick up Python much more quickly than, say, C. However, Python's inherent approachability also … [Read more...] about An Easier Way to Keep Old Python Code Healthy and Secure