I was recently able to grab some time with a Cisco customer to hear about their experience with Cisco Stealthwatch Cloud, a SaaS-based Network Detection and Response (NDR) solution. Aspire Technology Partners, a Managed Security Service Provider, explained their use of the product for one of its customers that was in a dangerous situation involving some slippery malware … [Read more...] about Stop playing whack-a-mole and put threats to rest with Cisco Stealthwatch Cloud
stop
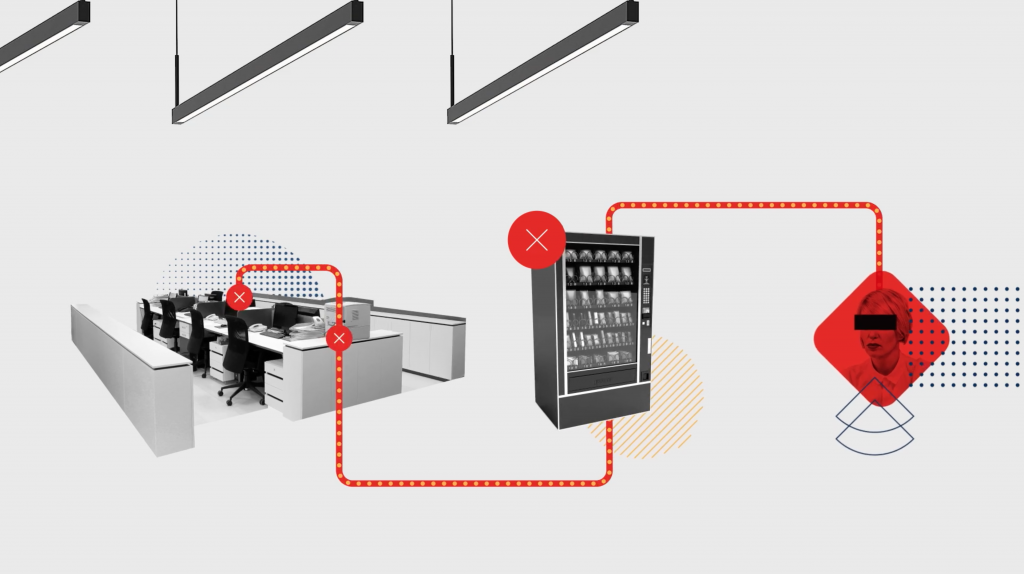
Are you ready to place a call for simplified cybersecurity? It’s time to stop switchboarding.
My grandfather was born in the 1930s. In the early 2000s, he used to recollect childhood memories of his experience with the telephone while growing up in India. Since the 1990s, advances in this industry have made communication a piece of cake. He would often tell us stories about day trips for the sole purpose of making a phone call, the community experience of the party … [Read more...] about Are you ready to place a call for simplified cybersecurity? It’s time to stop switchboarding.
We Stop. So You Can Go.
In March 2020, at the beginning of the U.S. response to the worldwide COVID-19 pandemic, I expressed my gratitude for the healthcare workers and other first responders who put themselves at risk to ensure the health and safety of us all during these unprecedented, challenging times. This gratitude is shared by all CrowdStrike® team members, who remain committed to our … [Read more...] about We Stop. So You Can Go.
Firefox Releases Critical Patch Update to Stop Ongoing Zero-Day Attacks
If you use the Firefox web browser, you need to update it right now.Mozilla earlier today released Firefox 67.0.3 and Firefox ESR 60.7.1 versions to patch a critical zero-day vulnerability in the browsing software that hackers have been found exploiting in the wild.Discovered and reported by Samuel Groß, a cybersecurity researcher at Google Project Zero, the vulnerability could … [Read more...] about Firefox Releases Critical Patch Update to Stop Ongoing Zero-Day Attacks