The U.S. Department of Justice (DoJ) on Monday unsealed indictments against seven Chinese nationals for their involvement in a hacking group that targeted U.S. and foreign critics, journalists, businesses, and political officials for about 14 years. The defendants include Ni Gaobin (倪高彬), Weng Ming (翁明), Cheng Feng (程锋), Peng Yaowen (彭耀文), Sun Xiaohui (孙小辉), Xiong Wang (熊旺), … [Read more...] about U.S. Charges 7 Chinese Nationals in Major 14-Year Cyber Espionage Operation
Chinese
Chinese Hackers Operate Undetected in U.S. Critical Infrastructure for Half a Decade
The U.S. government on Wednesday said the Chinese state-sponsored hacking group known as Volt Typhoon had been embedded into some critical infrastructure networks in the country for at least five years. Targets of the threat actor include communications, energy, transportation, and water and wastewater systems sectors in the U.S. and Guam. "Volt Typhoon's choice of targets and … [Read more...] about Chinese Hackers Operate Undetected in U.S. Critical Infrastructure for Half a Decade
Malicious Ads on Google Target Chinese Users with Fake Messaging Apps
Jan 26, 2024NewsroomMalvertising / Phishing-as-a-service Chinese-speaking users have been targeted by malicious Google ads for restricted messaging apps like Telegram as part of an ongoing malvertising campaign. "The threat actor is abusing Google advertiser accounts to create malicious ads and pointing them to pages where unsuspecting users will download Remote … [Read more...] about Malicious Ads on Google Target Chinese Users with Fake Messaging Apps
Chinese Hackers Silently Weaponized VMware Zero-Day Flaw for 2 Years
Jan 20, 2024NewsroomZero Day / Cyber Espionage An advanced China-nexus cyber espionage group previously linked to the exploitation of security flaws in VMware and Fortinet appliances has been linked to the abuse of a critical vulnerability in VMware vCenter Server as a zero-day since late 2021. "UNC3886 has a track record of utilizing zero-day vulnerabilities to complete … [Read more...] about Chinese Hackers Silently Weaponized VMware Zero-Day Flaw for 2 Years
Chinese Hackers Exploited New Zero-Day in Barracuda’s ESG Appliances
Dec 27, 2023NewsroomZero-Day / Email Security Barracuda has revealed that Chinese threat actors exploited a new zero-day in its Email Security Gateway (ESG) appliances to deploy backdoor on a "limited number" of devices. Tracked as CVE-2023-7102, the issue relates to a case of arbitrary code execution that resides within a third-party and open-source library … [Read more...] about Chinese Hackers Exploited New Zero-Day in Barracuda’s ESG Appliances
Chinese Hackers Target Semiconductor Firms in East Asia with Cobalt Strike
Oct 06, 2023NewsroomCyber Attack / Malware Threat actors have been observed targeting semiconductor companies in East Asia with lures masquerading as Taiwan Semiconductor Manufacturing Company (TSMC) that are designed to deliver Cobalt Strike beacons. The intrusion set, per EclecticIQ, leverages a backdoor called HyperBro, which is then used as a conduit to deploy the … [Read more...] about Chinese Hackers Target Semiconductor Firms in East Asia with Cobalt Strike
Encryption Flaws in Popular Chinese Language App Put Users’ Typed Data at Risk
Aug 10, 2023THNPrivacy / Encryption A widely used Chinese language input app for Windows and Android has been found vulnerable to serious security flaws that could allow a malicious interloper to decipher the text typed by users. The findings from the University of Toronto's Citizen Lab, which carried out an analysis of the encryption mechanism used in Tencent's Sogou Input … [Read more...] about Encryption Flaws in Popular Chinese Language App Put Users’ Typed Data at Risk
Chinese Hacker Group ‘Flea’ Targets American Ministries with Graphican Backdoor
Jun 21, 2023Ravie LakshmananCyber Threat / APT Foreign affairs ministries in the Americas have been targeted by a Chinese state-sponsored actor named Flea as part of a recent campaign that spanned from late 2022 to early 2023. The cyber attacks, per Broadcom's Symantec, involved a new backdoor codenamed Graphican. Some of the other targets included a government finance … [Read more...] about Chinese Hacker Group ‘Flea’ Targets American Ministries with Graphican Backdoor
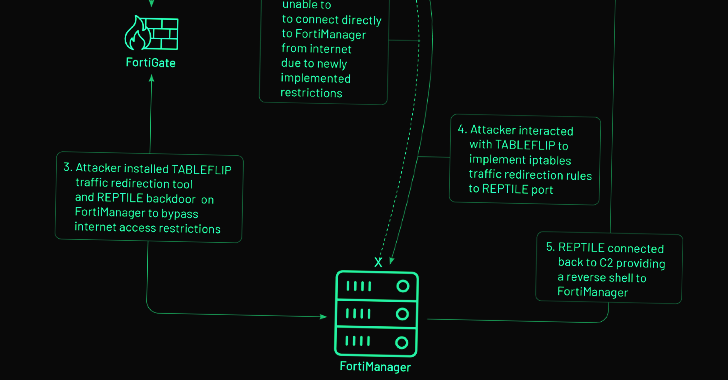
Chinese Hackers Exploit Fortinet Zero-Day Flaw for Cyber Espionage Attack
Mar 18, 2023Ravie LakshmananNetwork Security / Cyber Espionage The zero-day exploitation of a now-patched medium-severity security flaw in the Fortinet FortiOS operating system has been linked to a suspected Chinese hacking group. Threat intelligence firm Mandiant, which made the attribution, said the activity cluster is part of a broader campaign designed to deploy backdoors … [Read more...] about Chinese Hackers Exploit Fortinet Zero-Day Flaw for Cyber Espionage Attack
Chinese Tonto Team Hackers’ Second Attempt to Target Cybersecurity Firm Group-IB Fails
Feb 13, 2023Ravie LakshmananCyber Threat Intelligence The advanced persistent threat (APT) actor known as Tonto Team carried out an unsuccessful attack on cybersecurity company Group-IB in June 2022. The Singapore-headquartered firm said that it detected and blocked malicious phishing emails originating from the group targeting its employees. It's also the second attack aimed … [Read more...] about Chinese Tonto Team Hackers’ Second Attempt to Target Cybersecurity Firm Group-IB Fails