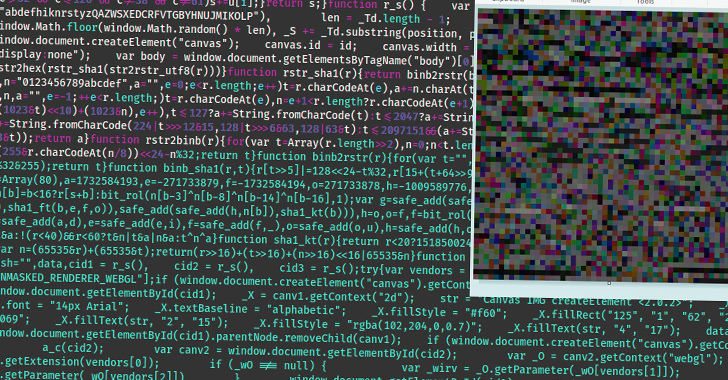
Aug 19, 2023THNMalvertising / Website Security Cybersecurity researchers have detailed an updated version of an advanced fingerprinting and redirection toolkit called WoofLocker that's engineered to conduct tech support scams. The sophisticated traffic redirection scheme was first documented by Malwarebytes in January 2020, leveraging JavaScript embedded in compromised … [Read more...] about WoofLocker Toolkit Hides Malicious Codes in Images to Run Tech Support Scams
Malicious
Identifying malicious Remote Desktop Protocol (RDP) connections with Elastic Security
Lateral movement is a dangerous threat in the landscape of highly integrated technologies. If attackers gain access to an endpoint, it’s critical for security teams to identify any and all movements they make. To combat this threat, Elastic Security is excited to announce a new lateral movement detection package that makes use of advanced analytics.In the past, we explored how … [Read more...] about Identifying malicious Remote Desktop Protocol (RDP) connections with Elastic Security
Dozens of malicious extensions for Google Chrome
Not so long ago, a few dozen malicious plugins were discovered in the Chrome Web Store (the official browser extension store for Google Chrome). The most popular of these extensions had over nine million downloads, and altogether these plugins had been downloaded around 87 million times. We explain what these extensions are and why they’re dangerous. Malicious extensions in the … [Read more...] about Dozens of malicious extensions for Google Chrome
GuLoader Malware Using Malicious NSIS Executables to Target E-Commerce Industry
Feb 06, 2023Ravie LakshmananCyber Attack / Endpoint Security E-commerce industries in South Korea and the U.S. are at the receiving end of an ongoing GuLoader malware campaign, cybersecurity firm Trellix disclosed late last month. The malspam activity is notable for transitioning away from malware-laced Microsoft Word documents to NSIS executable files for loading the … [Read more...] about GuLoader Malware Using Malicious NSIS Executables to Target E-Commerce Industry
APT Hackers Turn to Malicious Excel Add-ins as Initial Intrusion Vector
Dec 28, 2022Ravie LakshmananMalware / Windows Security Microsoft's decision to block Visual Basic for Applications (VBA) macros by default for Office files downloaded from the internet has led many threat actors to improvise their attack chains in recent months. Now according to Cisco Talos, advanced persistent threat (APT) actors and commodity malware families alike are … [Read more...] about APT Hackers Turn to Malicious Excel Add-ins as Initial Intrusion Vector
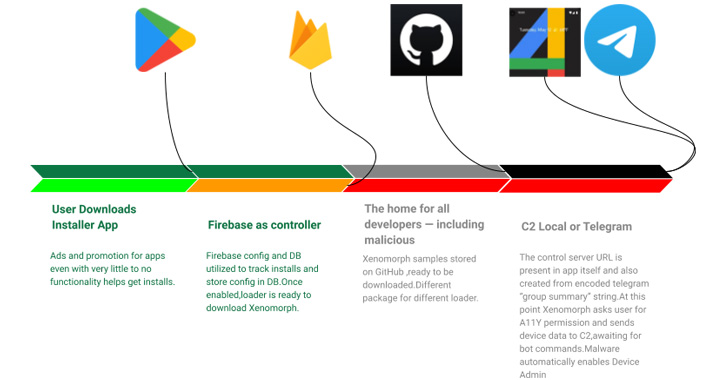
Malicious Google Play Store App Spotted Distributing Xenomorph Banking Trojan
Google has removed two new malicious dropper apps that have been detected on the Play Store for Android, one of which posed as a lifestyle app and was caught distributing the Xenomorph banking malware. "Xenomorph is a trojan that steals credentials from banking applications on users' devices," Zscaler ThreatLabz researchers Himanshu Sharma and Viral Gandhi said in an analysis … [Read more...] about Malicious Google Play Store App Spotted Distributing Xenomorph Banking Trojan
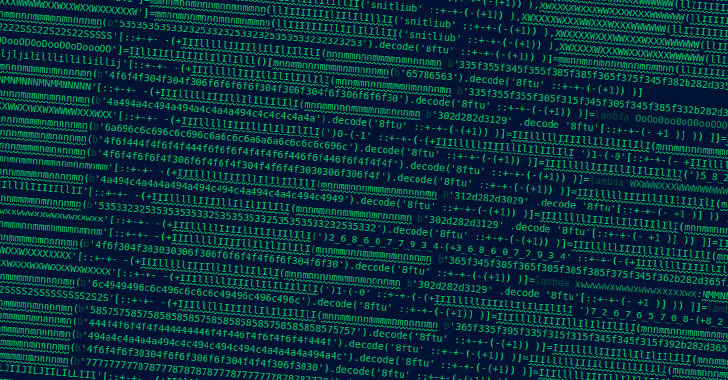
Researchers Uncover 29 Malicious PyPI Packages Targeted Developers with W4SP Stealer
Cybersecurity researchers have uncovered 29 packages in Python Package Index (PyPI), the official third-party software repository for the Python programming language, that aim to infect developers' machines with a malware called W4SP Stealer. "The main attack seems to have started around October 12, 2022, slowly picking up steam to a concentrated effort around October 22," … [Read more...] about Researchers Uncover 29 Malicious PyPI Packages Targeted Developers with W4SP Stealer
Researchers Detail Malicious Tools Used by Cyberespionage Group Earth Aughisky
A new piece of research has detailed the increasingly sophisticated nature of the malware toolset employed by an advanced persistent threat (APT) group named Earth Aughisky. "Over the last decade, the group has continued to make adjustments in the tools and malware deployments on specific targets located in Taiwan and, more recently, Japan," Trend Micro disclosed in a technical … [Read more...] about Researchers Detail Malicious Tools Used by Cyberespionage Group Earth Aughisky
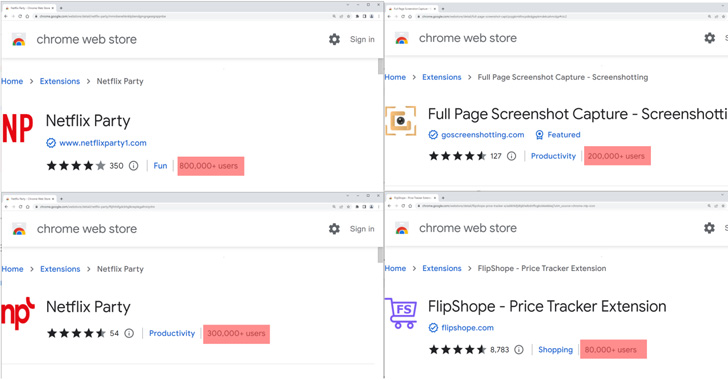
Experts Find Malicious Cookie Stuffing Chrome Extensions Used by 1.4 Million Users
Five imposter extensions for the Google Chrome web browser masquerading as Netflix viewers and others have been found to track users' browsing activity and profit of retail affiliate programs. "The extensions offer various functions such as enabling users to watch Netflix shows together, website coupons, and taking screenshots of a website," McAfee researchers Oliver Devane and … [Read more...] about Experts Find Malicious Cookie Stuffing Chrome Extensions Used by 1.4 Million Users
New Orchard Botnet Uses Bitcoin Founder’s Account Info to Generate Malicious Domains
A new botnet named Orchard has been observed using Bitcoin creator Satoshi Nakamoto's account transaction information to generate domain names to conceal its command-and-control (C2) infrastructure. "Because of the uncertainty of Bitcoin transactions, this technique is more unpredictable than using the common time-generated [domain generation algorithms], and thus more … [Read more...] about New Orchard Botnet Uses Bitcoin Founder’s Account Info to Generate Malicious Domains