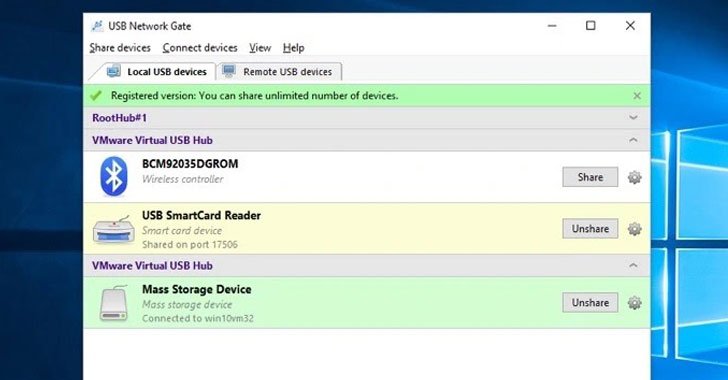
Cybersecurity researchers have disclosed multiple vulnerabilities in a third-party driver software developed by Eltima that have been "unwittingly inherited" by cloud desktop solutions like Amazon Workspaces, Accops, and NoMachine and could provide attackers a path to perform an array of malicious activities. "These vulnerabilities allow attackers to escalate privileges … [Read more...] about Eltima SDK Contain Multiple Vulnerabilities Affecting Several Cloud Service Provides
Vulnerabilities
Three dangerous vulnerabilities in Google Chrome
Google has released an emergency update for the Chrome browser that addresses three vulnerabilities: CVE-2021-37974, CVE-2021-37975, and CVE-2021-37976. Google experts consider one of the vulnerabilities as critical and the other two as highly dangerous. What’s worse: according to Google cybercriminals have already exploited two of these three vulnerabilities. Therefore, Google … [Read more...] about Three dangerous vulnerabilities in Google Chrome
Wake up! Identify API Vulnerabilities Proactively, From Production Back to Code
After more than 20 years in the making, now it's official: APIs are everywhere. In a 2021 survey, 73% of enterprises reported that they already publish more than 50 APIs, and this number is constantly growing. APIs have crucial roles to play in virtually every industry today, and their importance is increasing steadily, as they move to the forefront of business strategies. This … [Read more...] about Wake up! Identify API Vulnerabilities Proactively, From Production Back to Code
The Vulnerabilities of the Past Are the Vulnerabilities of the Future
Major software vulnerabilities are a fact of life, as illustrated by the fact that Microsoft has patched between 55 and 110 vulnerabilities each month this year – with 7% to 17% of those vulnerabilities being critical. May had the fewest vulnerabilities, with a total of 55 and only four considered critical. The problem is that the critical vulnerabilities are things we have … [Read more...] about The Vulnerabilities of the Past Are the Vulnerabilities of the Future
New NAME:WRECK Vulnerabilities Impact Nearly 100 Million IoT Devices
Security researchers have uncovered nine vulnerabilities affecting four TCP/IP stacks impacting more than 100 million consumer and enterprise devices that could be exploited by an attacker to take control of a vulnerable system. Dubbed "NAME:WRECK" by Forescout and JSOF, the flaws are the latest in series of studies undertaken as part of an initiative called Project Memoria to … [Read more...] about New NAME:WRECK Vulnerabilities Impact Nearly 100 Million IoT Devices
3 New Severe Security Vulnerabilities Found In SolarWinds Software
Cybersecurity researchers on Wednesday disclosed three severe security vulnerabilities impacting SolarWinds products, the most severe of which could have been exploited to achieve remote code execution with elevated privileges. Two of the flaws (CVE-2021-25274 and CVE-2021-25275) were identified in the SolarWinds Orion Platform, while a third separate weakness (CVE-2021-25276) … [Read more...] about 3 New Severe Security Vulnerabilities Found In SolarWinds Software
Researchers Find Vulnerabilities in Microsoft Azure Cloud Service
As businesses are increasingly migrating to the cloud, securing the infrastructure has never been more important. Now according to the latest research, two security flaws in Microsoft's Azure App Services could have enabled a bad actor to carry out server-side request forgery (SSRF) attacks or execute arbitrary code and take over the administration server. "This enables an … [Read more...] about Researchers Find Vulnerabilities in Microsoft Azure Cloud Service
Identify CVE-2020-1472 Vulnerabilities with Zerologon Dashboard
A serious and potentially dire patch warning has been issued by the Department of Homeland Security (DHS) advisory team, the Cybersecurity and Infrastructure Security Agency (CISA). The alert, labeled “Emergency Directive 20-04,” is based on vulnerability CVE-2020-1472 and requires U.S. federal agencies to immediately patch Microsoft Windows servers. Because of the severe … [Read more...] about Identify CVE-2020-1472 Vulnerabilities with Zerologon Dashboard
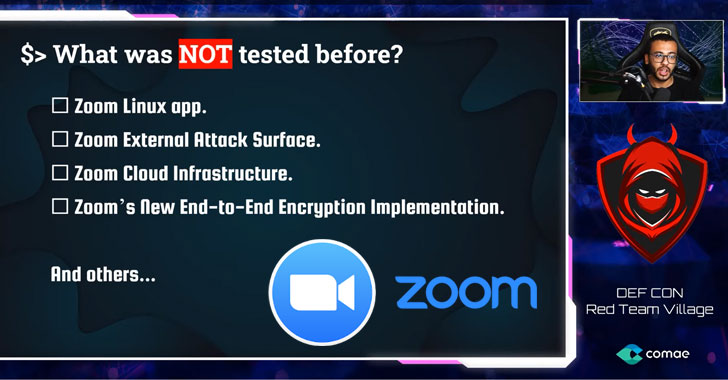
Researcher Demonstrates Several Zoom Vulnerabilities at DEF CON 28
Popular video conferencing app Zoom has addressed several security vulnerabilities, two of which affect its Linux client that could have allowed an attacker with access to a compromised system to read and exfiltrate Zoom user data—and even run stealthy malware as a sub-process of a trusted application.According to cybersecurity researcher Mazin Ahmed, who presented his findings … [Read more...] about Researcher Demonstrates Several Zoom Vulnerabilities at DEF CON 28
Ripple20: Critical Vulnerabilities Might be Putting Your IoT/OT Devices at Risk
Cybersecurity researchers from JSOF have just published a set of 19 vulnerabilities, dubbed Ripple20 that are impacting the TCP/IP stack developed by Treck. This software stack is integrated into millions of systems used in the healthcare, transportation, manufacturing, telecoms and energy markets, potentially affecting a very large number of organizations and critical … [Read more...] about Ripple20: Critical Vulnerabilities Might be Putting Your IoT/OT Devices at Risk