Apr 26, 2023Ravie LakshmananServer Security / Vulnerability The maintainers of the Apache Superset open source data visualization software have released fixes to plug an insecure default configuration that could lead to remote code execution. The vulnerability, tracked as CVE-2023-27524 (CVSS score: 8.9), impacts versions up to and including 2.0.1 and relates to the use of a … [Read more...] about Insecure Default Configuration Exposes Servers to RCE Attacks
attacks
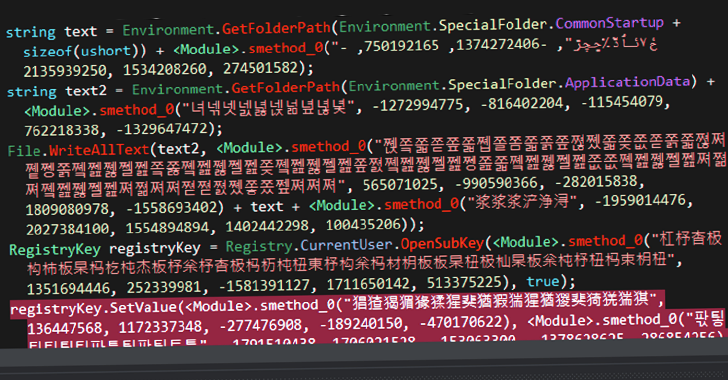
Russia-Linked Hackers Launches Espionage Attacks on Foreign Diplomatic Entities
Apr 14, 2023Ravie LakshmananUnited States The Russia-linked APT29 (aka Cozy Bear) threat actor has been attributed to an ongoing cyber espionage campaign targeting foreign ministries and diplomatic entities located in NATO member states, the European Union, and Africa. According to Poland's Military Counterintelligence Service and the CERT Polska team, the observed activity … [Read more...] about Russia-Linked Hackers Launches Espionage Attacks on Foreign Diplomatic Entities
Iran-Based Hackers Caught Carrying Out Destructive Attacks Under Ransomware Guise
Apr 08, 2023Ravie LakshmananCyber War / Cyber Threat The Iranian nation-state group known as MuddyWater has been observed carrying out destructive attacks on hybrid environments under the guise of a ransomware operation. That's according to new findings from the Microsoft Threat Intelligence team, which discovered the threat actor targeting both on-premises and cloud … [Read more...] about Iran-Based Hackers Caught Carrying Out Destructive Attacks Under Ransomware Guise
New ScrubCrypt Crypter Used in Cryptojacking Attacks Targeting Oracle WebLogic
Mar 09, 2023Ravie LakshmananCryptojacking / Threat Detection, The infamous cryptocurrency miner group called 8220 Gang has been observed using a new crypter called ScrubCrypt to carry out cryptojacking operations. According to Fortinet FortiGuard Labs, the attack chain commences with successful exploitation of susceptible Oracle WebLogic servers to download a PowerShell … [Read more...] about New ScrubCrypt Crypter Used in Cryptojacking Attacks Targeting Oracle WebLogic
Why You Need AI and Machine Learning to Combat Hands-on-Keyboard Attacks
Malware gets the headlines, but the bigger threat is hands-on-keyboard adversary activity which can evade traditional security solutions and present detection challenges Machine learning (ML) can predict and proactively protect against emerging threats by using behavioral event data. CrowdStrike’s artificial intelligence (AI)-powered indicators of attack (IOAs) use ML to detect … [Read more...] about Why You Need AI and Machine Learning to Combat Hands-on-Keyboard Attacks
How cybercriminals tailor attacks for different age groups of gamers
These days, a 12 or 13-year-old kid can become a professional eSports player, while the youngest of them began his career at the ripe old age of… four! The gaming world has become much younger, but all gamers — both children and adults — face multiple cyberthreats. And scammers tailor each of their schemes with a particular age audience in mind. Although children spend less … [Read more...] about How cybercriminals tailor attacks for different age groups of gamers
Using Artificial Intelligence and Machine Learning to Combat Hands-on-Keyboard Cybersecurity Attacks
Malware gets the headlines, but the bigger threat is hands-on-keyboard adversary activity which can evade traditional security solutions and present detection challenges Machine learning (ML) can predict and proactively protect against emerging threats by using behavioral event data. CrowdStrike’s artificial intelligence (AI)-powered indicators of attack (IOAs) use ML to detect … [Read more...] about Using Artificial Intelligence and Machine Learning to Combat Hands-on-Keyboard Cybersecurity Attacks
Threat Actors Adopt Havoc Framework for Post-Exploitation in Targeted Attacks
Feb 22, 2023Ravie LakshmananExploitation Framework / Cyber Threat An open source command-and-control (C2) framework known as Havoc is being adopted by threat actors as an alternative to other well-known legitimate toolkits like Cobalt Strike, Sliver, and Brute Ratel. Cybersecurity firm Zscaler said it observed a new campaign in the beginning of January 2023 targeting an … [Read more...] about Threat Actors Adopt Havoc Framework for Post-Exploitation in Targeted Attacks
Samsung Introduces New Feature to Protect Users from Zero-Click Malware Attacks
Feb 20, 2023Ravie LakshmananMobile Security / Zero Day Samsung has announced a new feature called Message Guard that comes with safeguards to protect users from malware and spyware via what's referred to as zero-click attacks. The South Korean chaebol said the solution "preemptively" secures users' devices by "limiting exposure to invisible threats disguised as image … [Read more...] about Samsung Introduces New Feature to Protect Users from Zero-Click Malware Attacks
CISA Warns of Active Attacks Exploiting Fortra MFT, TerraMaster NAS, and Intel Driver Flaws
Feb 11, 2023Ravie LakshmananThreat Response / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added three flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active abuse in the wild. Included among the three is CVE-2022-24990, a bug affecting TerraMaster network-attached storage (TNAS) devices that could … [Read more...] about CISA Warns of Active Attacks Exploiting Fortra MFT, TerraMaster NAS, and Intel Driver Flaws