Customer engagement platform Twilio on Monday disclosed that a "sophisticated" threat actor gained "unauthorized access" using an SMS-based phishing campaign aimed at its staff to gain information on a "limited number" of accounts. The social-engineering attack was bent on stealing employee credentials, the company said, calling the as-yet-unidentified adversary … [Read more...] about Twilio Suffers Data Breach After Employees Fall Victim to SMS Phishing Attack
Breach
TikTok Postpones Privacy Policy Update in Europe After Italy Warns of GDPR Breach
Popular video-sharing platform TikTok on Tuesday agreed to pause a controversial privacy policy update that could have allowed it to serve targeted ads based on users' activity on the social video platform without their permission to do so. The reversal, reported by TechCrunch, comes a day after the Italian data protection authority — the Garante per la Protezione dei Dati … [Read more...] about TikTok Postpones Privacy Policy Update in Europe After Italy Warns of GDPR Breach
Latest Atlassian Confluence Flaw Exploited to Breach Jenkins Project Server
The maintainers of Jenkins—a popular open-source automation server software—have disclosed a security breach after unidentified threat actors gained access to one of their servers by exploiting a recently disclosed vulnerability in Atlassian Confluence service to install a cryptocurrency miner. The "successful attack," which is believed to have occurred last week, was mounted … [Read more...] about Latest Atlassian Confluence Flaw Exploited to Breach Jenkins Project Server
Anatomy of a Breach: Preventing the Next Advanced Attack
Your company’s stock price nosedives by 15% in a single day. You get a flood of messages from concerned family and friends about your company. Your company’s name is all over the news. Your colleagues exchange hundreds of frantic messages while trying to figure out what happened and how to respond. This is what it looks like when your organization is breached. I know this from … [Read more...] about Anatomy of a Breach: Preventing the Next Advanced Attack
SolarWinds Hackers Breach Microsoft Customer Support to Target its Customers
In yet another sign that the Russian hackers who breached SolarWinds network monitoring software to compromise a slew of entities never really went away, Microsoft said the threat actor behind the malicious cyber activities used password spraying and brute-force attacks in an attempt to guess passwords and gain access to its customer accounts. "This recent activity was mostly … [Read more...] about SolarWinds Hackers Breach Microsoft Customer Support to Target its Customers
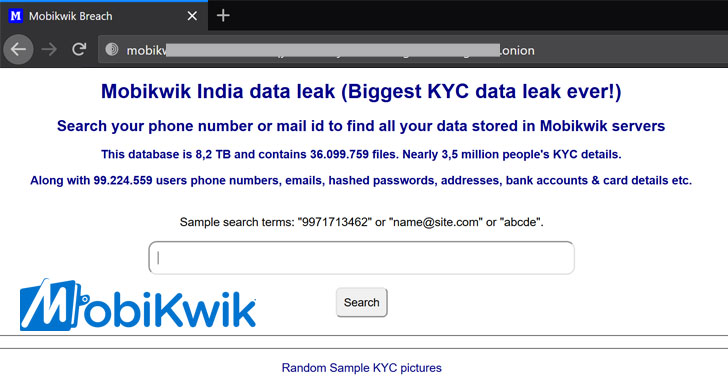
MobiKwik Suffers Major Breach — KYC Data of 3.5 Million Users Exposed
Popular Indian mobile payments service MobiKwik on Monday came under fire after 8.2 terabytes (TB) of data belonging to millions of its users began circulating on the dark web in the aftermath of a major data breach that came to light earlier this month. The leaked data includes sensitive personal information such as:customer names,hashed passwords,email addresses,residential … [Read more...] about MobiKwik Suffers Major Breach — KYC Data of 3.5 Million Users Exposed
Data Breach Exposes 1.6 Million Jobless Claims Filed in the Washington State
The Office of the Washington State Auditor (SAO) on Monday said it's investigating a security incident that resulted in the compromise of personal information of more than 1.6 million people who filed for unemployment claims in the state in 2020. The SAO blamed the breach on a software vulnerability in Accellion's File Transfer Appliance (FTA) service, which allows … [Read more...] about Data Breach Exposes 1.6 Million Jobless Claims Filed in the Washington State
The SolarWinds Orion Breach, and What You Should Know
By Joe Marshall of Cisco Talos and Paul Smith of Cisco IoT What is this? On December 11th, 2020, the U.S. government and the company SolarWinds disclosed a breach into their SolarWinds Orion Platform network management software. This attack was conducted by a sophisticated and likely nation-state based attacker. SolarWinds Orion is a commonly used network management software … [Read more...] about The SolarWinds Orion Breach, and What You Should Know
FireEye Breach Detection Guidance – Cisco Blogs
Cisco Blogs / Security / Threat Research / FireEye Breach Detection Guidance Cyber security firm FireEye recently disclosed an incident that was reported to have resulted in the inadvertent disclosure of various internally developed offensive security tools (OSTs) that were used across FireEye red-team engagements. Some of these tools appear to be based on … [Read more...] about FireEye Breach Detection Guidance – Cisco Blogs
(Live) Webinar – XDR and Beyond with Autonomous Breach Protection
Anyone paying attention to the cybersecurity technology market has heard the term XDR - Extended Detection and Response.XDR is a new technology approach that combines multiple protection technologies into a single platform. All the analyst firms are writing about it, and many of the top cybersecurity companies are actively moving into this space.Why is XDR receiving all the … [Read more...] about (Live) Webinar – XDR and Beyond with Autonomous Breach Protection