Researchers have detailed what they call the "first successful attempt" at decrypting data infected with Hive ransomware without relying on the private key used to lock access to the content. "We were able to recover the master key for generating the file encryption key without the attacker's private key, by using a cryptographic vulnerability identified through analysis," a … [Read more...] about Master Key for Hive Ransomware Retrieved Using a Flaw in its Encryption Algorithm
encryption
Patching the CentOS 8 Encryption Bug is Urgent – What Are Your Plans?
There are three things you can be sure of in life: death, taxes – and new CVEs. For organizations that rely on CentOS 8, the inevitable has now happened, and it didn't take long. Just two weeks after reaching the official end of life, something broke spectacularly, leaving CentOS 8 users at major risk of a severe attack – and with no support from CentOS. You'd think that this … [Read more...] about Patching the CentOS 8 Encryption Bug is Urgent – What Are Your Plans?
LockFile Ransomware Bypasses Protection Using Intermittent File Encryption
A new ransomware family that emerged last month comes with its own bag of tricks to bypass ransomware protection by leveraging a novel technique called "intermittent encryption." Called LockFile, the operators of the ransomware has been found exploiting recently disclosed flaws such as ProxyShell and PetitPotam to compromise Windows servers and deploy file-encrypting malware … [Read more...] about LockFile Ransomware Bypasses Protection Using Intermittent File Encryption
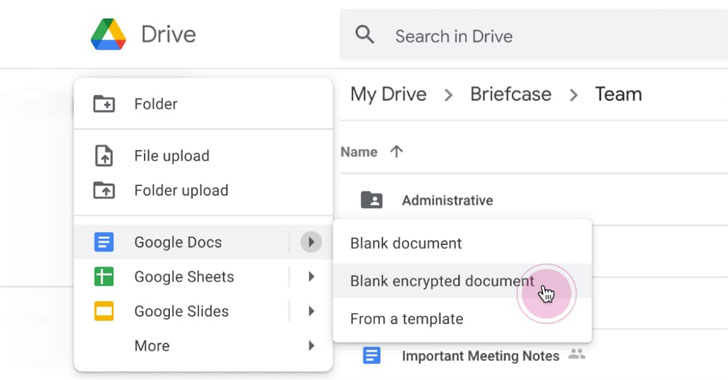
Google Workspace Now Offers Client-side Encryption For Drive and Docs
Google on Monday announced that it's rolling out client-side encryption to Google Workspace (formerly G Suite), thereby giving its enterprise customers direct control of encryption keys and the identity service they choose to access those keys. "With client-side encryption, customer data is indecipherable to Google, while users can continue to take advantage of Google's native … [Read more...] about Google Workspace Now Offers Client-side Encryption For Drive and Docs
Future Focused: Encryption and Visibility Can Co-Exist
Privacy and security are in constant tension. Hiding internet activity strengthens privacy—but also makes it easier for bad actors to infiltrate the network. In fact, 63% of threats detected by Cisco Stealthwatch in 2019 were in encrypted traffic. The European Union is concerned enough that it drafted a resolution in November 2020 to ban end-to-end encryption, prompting outcry … [Read more...] about Future Focused: Encryption and Visibility Can Co-Exist
Network Security Efficacy in the Age of Pervasive TLS Encryption
A Reality Check on Firewall Visibility One question which I love to ask next-generation firewall (NGFW) and intrusion prevention system (IPS) administrators is whether they have seen a gradual decline in their deployments’ security efficacy over the last few years. Most answer this question with a resounding “yes,” and then wonder how I knew. With over 90% of Internet traffic … [Read more...] about Network Security Efficacy in the Age of Pervasive TLS Encryption
New Raccoon Attack Could Let Attackers Break SSL/TLS Encryption
A group of researchers has detailed a new timing vulnerability in Transport Layer Security (TLS) protocol that could potentially allow an attacker to break the encryption and read sensitive communication under specific conditions.Dubbed "Raccoon Attack," the server-side attack exploits a side-channel in the cryptographic protocol (versions 1.2 and lower) to extract the shared … [Read more...] about New Raccoon Attack Could Let Attackers Break SSL/TLS Encryption
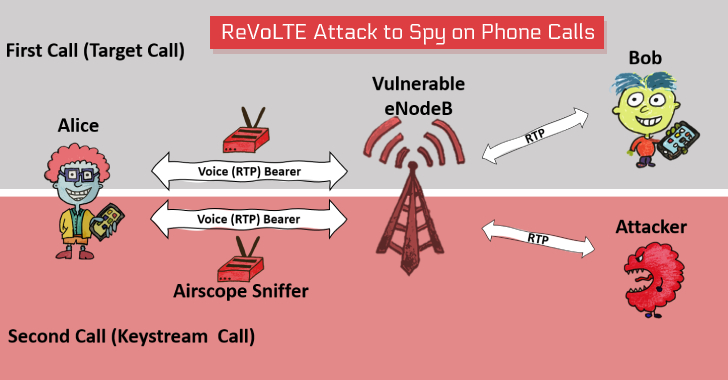
New Attack Lets Hackers Decrypt VoLTE Encryption to Spy on Phone Calls
A team of academic researchers—who previously made the headlines earlier this year for uncovering severe security issues in the 4G LTE and 5G networks—today presented a new attack called 'ReVoLTE,' that could let remote attackers break the encryption used by VoLTE voice calls and spy on targeted phone calls.The attack doesn't exploit any flaw in the Voice over LTE (VoLTE) … [Read more...] about New Attack Lets Hackers Decrypt VoLTE Encryption to Spy on Phone Calls
MongoDB 4.2 Introduces End-to-End Field Level Encryption for Databases
At its developer conference held earlier this week in New York, the MongoDB team announced the latest version of its database management software that includes a variety of advanced features, including Field Level Encryption, Distributed Transactions, and Wildcard Indexes.The newly introduced Field Level Encryption (FLE), which will be available in the upcoming MongoDB 4.2 … [Read more...] about MongoDB 4.2 Introduces End-to-End Field Level Encryption for Databases