Jul 06, 2023The Hacker News Gcore Radar is a quarterly report prepared by Gcore that provides insights into the current state of the DDoS protection market and cybersecurity trends. This report offers you an understanding of the evolving threat landscape and highlights the measures required to protect against attacks effectively. It serves as an insight for businesses and … [Read more...] about Gain Insights from Gcore’s 2023 DDoS Attack Statistics
Gain
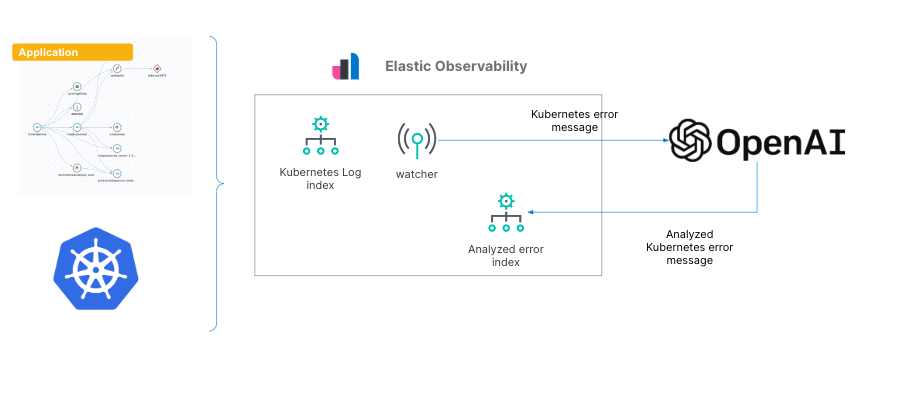
Gain insights into Kubernetes errors with Elastic Observability logs and OpenAI
As we’ve shown in previous blogs, Elastic® provides a way to ingest and manage telemetry from the Kubernetes cluster and the application running on it. Elastic provides out-of-the-box dashboards to help with tracking metrics, log management and analytics, APM functionality (which also supports native OpenTelemetry), and the ability to analyze everything with AIOps features and … [Read more...] about Gain insights into Kubernetes errors with Elastic Observability logs and OpenAI
Researchers Detail Azure SFX Flaw That Could’ve Allowed Attackers to Gain Admin Access
Cybersecurity researchers have shared more details about a now-patched security flaw in Azure Service Fabric Explorer (SFX) that could potentially enable an attacker to gain administrator privileges on the cluster. The vulnerability, tracked as CVE-2022-35829, carries a CVSS severity rating of 6.2 and was addressed by Microsoft as part of its Patch Tuesday updates last … [Read more...] about Researchers Detail Azure SFX Flaw That Could’ve Allowed Attackers to Gain Admin Access
This New Android Malware Can Gain Root Access to Your Smartphones
An unidentified threat actor has been linked to a new Android malware strain that features the ability to root smartphones and take complete control over infected smartphones while simultaneously taking steps to evade detection. The malware has been named "AbstractEmu" owing to its use of code abstraction and anti-emulation checks to avoid running while under analysis. Notably, … [Read more...] about This New Android Malware Can Gain Root Access to Your Smartphones
Three ways ISE 3.0 enables visibility-driven network segmentation to gain zero trust
ISE 3.0 – Control access and contain threats within zones of trust You wake up to find out that another security incident has occurred. You are confused and not sure how the attacker was able to get by your perimeter. But then you realize you haven’t had a perimeter for some time as it has been pulled apart by cloud, mobility, and IoT. Like your network resources, your … [Read more...] about Three ways ISE 3.0 enables visibility-driven network segmentation to gain zero trust
A Bug in Facebook Messenger for Windows Could’ve Helped Malware Gain Persistence
Cybersecurity researchers at Reason Labs, the threat research arm of security solutions provider Reason Cybersecurity, today disclosed details of a vulnerability they recently discovered in the Facebook Messenger application for Windows.The vulnerability, which resides in Messenger version 460.16, could allow attackers to leverage the app to potentially execute malicious files … [Read more...] about A Bug in Facebook Messenger for Windows Could’ve Helped Malware Gain Persistence
How to gain visibility into Mobile Devices
Introduction Falcon for Mobile is CrowdStrike’s EDR solution on mobile devices. Falcon for Mobile monitors and records activities taking place on Android and iOS, providing the visibility necessary to detect attackers, malicious insider activity, and corporate data leakage Falcon for Mobile allows organizations to benefit from powerful reporting, investigation, and threat … [Read more...] about How to gain visibility into Mobile Devices
Threat Hunting: How to Gain the Most Value
Sean Mason, Director of Cisco Incident Response Services andJeff Bollinger, Investigations Manager, Cisco Security Incident Response Team (CSIRT) As security practitioners who continuously look for adversarial malice, one of the questions we are asked frequently is: What’s around the corner? Threat actors evolve over time, so how do we know not only what they’re doing now, but … [Read more...] about Threat Hunting: How to Gain the Most Value
Gain the Trust of Your Business Customers With SOC 2 Compliance
In today's business environment, data is what matters most. It matters to organizations that monetize it into operational insights and optimisations, and it matters the threat actors that relentlessly seek to achieve similar monetisation by compromising it.In the very common scenario in which organisation A provides services to organization B, it’s imperative for the latter to … [Read more...] about Gain the Trust of Your Business Customers With SOC 2 Compliance