There are three things you can be sure of in life: death, taxes – and new CVEs. For organizations that rely on CentOS 8, the inevitable has now happened, and it didn't take long. Just two weeks after reaching the official end of life, something broke spectacularly, leaving CentOS 8 users at major risk of a severe attack – and with no support from CentOS. You'd think that this … [Read more...] about Patching the CentOS 8 Encryption Bug is Urgent – What Are Your Plans?
information security
How to See More, But Respond Less with Enhanced Threat Visibility
The subject of threat visibility is a recurring one in cybersecurity. With an expanding attack surface due to the remote work transformation, cloud and SaaS computing and the proliferation of personal devices, seeing all the threats that are continuously bombarding the company is beyond challenging. This especially rings true for small to medium-sized enterprises with limited … [Read more...] about How to See More, But Respond Less with Enhanced Threat Visibility
Hackers Exploited MSHTML Flaw to Spy on Government and Defense Targets
Cybersecurity researchers on Tuesday took the wraps off a multi-stage espionage campaign targeting high-ranking government officials overseeing national security policy and individuals in the defense industry in Western Asia. The attack is unique as it leverages Microsoft OneDrive as a command-and-control (C2) server and is split into as many as six stages to stay as hidden as … [Read more...] about Hackers Exploited MSHTML Flaw to Spy on Government and Defense Targets
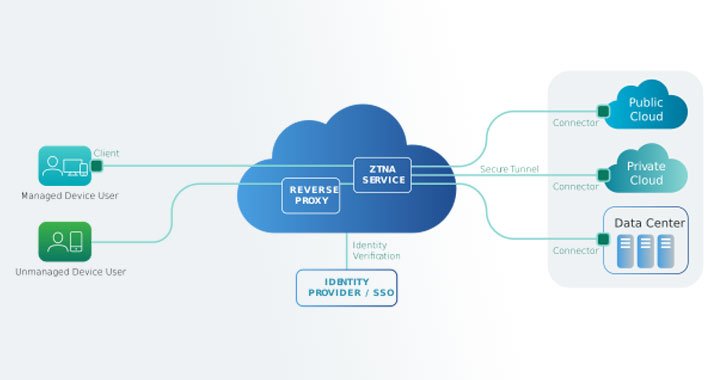
ZTNAs Address Requirements VPNs Cannot. Here’s Why.
I recently hopped on the Lookout podcast to talk about virtual private networks (VPNs) and how they've been extended beyond their original use case of connecting remote laptops to your corporate network. Even in this new world where people are using personal devices and cloud apps, VPN continues to be the go-to solution for remote access and cloud access. After my conversation … [Read more...] about ZTNAs Address Requirements VPNs Cannot. Here’s Why.
Hackers Attempt to Exploit New SolarWinds Serv-U Bug in Log4Shell Attacks
Microsoft on Wednesday disclosed details of a new security vulnerability in SolarWinds Serv-U software that it said was being weaponized by threat actors to propagate attacks leveraging the Log4j flaws to compromise targets. Tracked as CVE-2021-35247 (CVSS score: 5.3), the issue is an "input validation vulnerability that could allow attackers to build a query given some input … [Read more...] about Hackers Attempt to Exploit New SolarWinds Serv-U Bug in Log4Shell Attacks
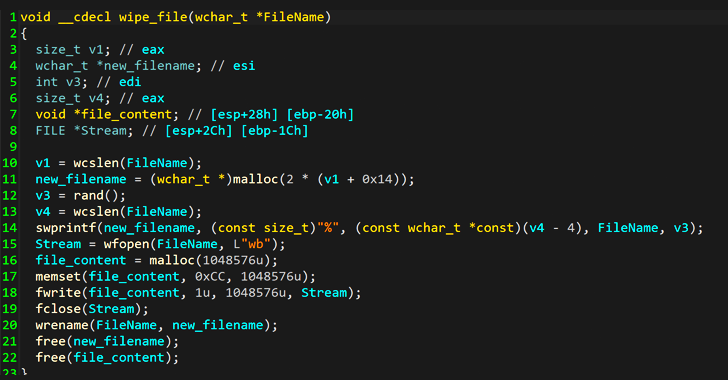
Experts Find Strategic Similarities b/w NotPetya and WhisperGate Attacks on Ukraine
Latest analysis into the wiper malware that targeted dozens of Ukrainian agencies earlier this month has revealed "strategic similarities" to NotPetya malware that was unleashed against the country's infrastructure and elsewhere in 2017. The malware, dubbed WhisperGate, was discovered by Microsoft last week, which said it observed the destructive cyber campaign targeting … [Read more...] about Experts Find Strategic Similarities b/w NotPetya and WhisperGate Attacks on Ukraine
Chinese Hackers Spotted Using New UEFI Firmware Implant in Targeted Attacks
A previously undocumented firmware implant deployed to maintain stealthy persistence as part of a targeted espionage campaign has been linked to the Chinese-speaking Winnti advanced persistent threat group (APT41). Kaspersky, which codenamed the rootkit MoonBounce, characterized the malware as the "most advanced UEFI firmware implant discovered in the wild to date," adding "the … [Read more...] about Chinese Hackers Spotted Using New UEFI Firmware Implant in Targeted Attacks
Google Details Two Zero-Day Bugs Reported in Zoom Clients and MMR Servers
An exploration of zero-click attack surface for the popular video conferencing solution Zoom has yielded two previously undisclosed security vulnerabilities that could have been exploited to crash the service, execute malicious code, and even leak arbitrary areas of its memory. Natalie Silvanovich of Google Project Zero, who discovered and reported the two flaws last year, said … [Read more...] about Google Details Two Zero-Day Bugs Reported in Zoom Clients and MMR Servers
Cyber Threat Protection — It All Starts with Visibility
Just as animals use their senses to detect danger, cybersecurity depends on sensors to identify signals in the computing environment that may signal danger. The more highly tuned, diverse and coordinated the senses, the more likely one is to detect important signals that indicate danger. This, however, can be a double-edged sword. Too many signals with too little advanced … [Read more...] about Cyber Threat Protection — It All Starts with Visibility
Don’t Use Public Wi-Fi Without DNS Filtering
Providing public Wi-Fi is a great service to offer your customers as it becomes more and more standard in today's society. I like the fact that I do not have to worry about accessing the Internet while I am away, or spending a lot of money on an international connection, or just staying offline while I am away. With public Wi-Fi, modern life has become a constant connection to … [Read more...] about Don’t Use Public Wi-Fi Without DNS Filtering