Trojan subscribers represent a time-honored method of relieving Android users of their hard-earned cash. They infiltrate a smartphone under the guise of useful apps and secretly subscribe to paid services. More often than not, the subscription itself is genuine, only the user most likely does not need the service. The creators of such Trojans make money on commission; that is, … [Read more...] about How Trojans take out paid subscriptions
paid
Insurance Firm CNA Financial Reportedly Paid Hackers $40 Million in Ransom
U.S. insurance giant CNA Financial reportedly paid $40 million to a ransomware gang to recover access to its systems following an attack in March, making it one the most expensive ransoms paid to date. The development was first reported by Bloomberg, citing "people with knowledge of the attack." The adversary that staged the intrusion is said to have allegedly demanded $60 … [Read more...] about Insurance Firm CNA Financial Reportedly Paid Hackers $40 Million in Ransom
Colonial Pipeline Paid Nearly $5 Million in Ransom to Cybercriminals
Colonial Pipeline on Thursday restored operations to its entire pipeline system nearly a week following a ransomware infection targeting its IT systems, forcing it to reportedly shell out nearly $5 million to regain control of its computer networks. "Following this restart, it will take several days for the product delivery supply chain to return to normal," the company said in … [Read more...] about Colonial Pipeline Paid Nearly $5 Million in Ransom to Cybercriminals
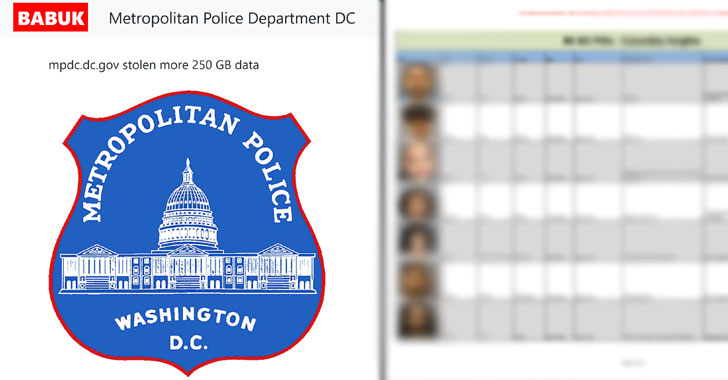
Hackers Threaten to Leak D.C. Police Informants’ Info If Ransom Is Not Paid
The Metropolitan Police Department (MPD) of the District of Columbia has become the latest high-profile government agency to fall victim to a ransomware attack. The Babuk Locker gang claimed in a post on the dark web that they had compromised the DC Police's networks and stolen 250 GB of unencrypted files. Screenshots shared by the group, and seen by The Hacker News, include … [Read more...] about Hackers Threaten to Leak D.C. Police Informants’ Info If Ransom Is Not Paid
Fleeceware and hidden paid subscriptions: How to protect yourself
Remember how Pulp Fiction hitman Vincent Vega wanted to try a milkshake simply because it cost a whopping $5? That’s a completely normal reaction — many people automatically associate high price with some extraordinary quality. So, if they can sample an expensive product free, even those who don’t plan to buy are interested. Some smartphone app developers take advantage of this … [Read more...] about Fleeceware and hidden paid subscriptions: How to protect yourself
Two Florida Cities Paid $1.1 Million to Ransomware Hackers This Month
In the last two weeks, Florida has paid more than $1.1 million in bitcoin to cybercriminals to recover encrypted files from two separate ransomware attacks—one against Riviera Beach and the other against Lake City.Lake City, a city in northern Florida, agreed on Monday to pay hackers 42 Bitcoin (equivalent to $573,300 at the current value) to unlock phone and email systems … [Read more...] about Two Florida Cities Paid $1.1 Million to Ransomware Hackers This Month
YouTube Launches Paid Channels, Subscriptions Start at $0.99/Month
YouTube has announced the launch of a new paid channels feature that lets content providers charge a subscription fee for access to their channels. … [Read more...] about YouTube Launches Paid Channels, Subscriptions Start at $0.99/Month