There’s no stopping when it comes to scaling your business, so why should your security remain stagnant? With your organization constantly expanding and your IT and security stack increasing in tools, your threat landscape is bound to grow with it. And by leveraging an increasing number of external applications and software-as-a-service (SaaS)-delivered solutions, you’re … [Read more...] about Unifying the Power of EDR with SaaS and Application Security
security
Attackers Can Remotely Disable Fortress Wi-Fi Home Security Alarms
New vulnerabilities have been discovered in Fortress S03 Wi-Fi Home Security System that could be potentially abused by a malicious party to gain unauthorized access with an aim to alter system behavior, including disarming the devices without the victim's knowledge. The two unpatched issues, tracked under the identifiers CVE-2021-39276 (CVSS score: 5.3) and CVE-2021-39277 … [Read more...] about Attackers Can Remotely Disable Fortress Wi-Fi Home Security Alarms
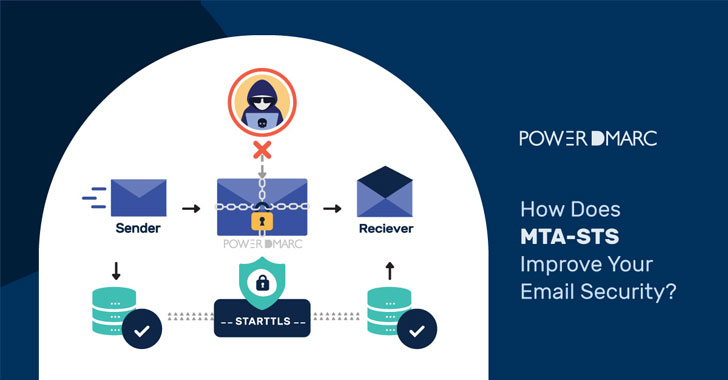
How Does MTA-STS Improve Your Email Security?
Simple Mail Transfer Protocol or SMTP has easily exploitable security loopholes. Email routing protocols were designed in a time when cryptographic technology was at a nascent stage (e.g., the de-facto protocol for email transfer, SMTP, is nearly 40 years old now), and therefore security was not an important consideration. As a result, in most email systems encryption is still … [Read more...] about How Does MTA-STS Improve Your Email Security?
Email Security Recommendations You Should Consider from 2021
With contributions from Jamal “Jay” Bethea, Cisco Secure Email Product Marketing Manager Think email security is not complicated; think again. Not only is email the #1 attack vector, but regulatory compliance requirements across sectors make it difficult to know which data protection laws are for your industry. Now mix in architectural changes that support cloud productivity … [Read more...] about Email Security Recommendations You Should Consider from 2021
Unpatched Security Flaws Expose Mitsubishi Safety PLCs to Remote Attacks
Multiple unpatched security vulnerabilities have been disclosed in Mitsubishi safety programmable logic controllers (PLCs) that could be exploited by an adversary to acquire legitimate user names registered in the module via a brute-force attack, unauthorizedly login to the CPU module, and even cause a denial-of-service (DoS) condition. The security weaknesses, disclosed by … [Read more...] about Unpatched Security Flaws Expose Mitsubishi Safety PLCs to Remote Attacks
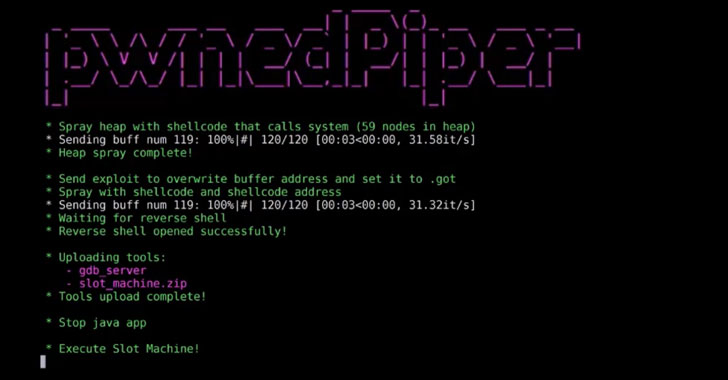
PwnedPiper PTS Security Flaws Threaten 80% of Hospitals in the U.S.
Cybersecurity researchers on Monday disclosed a set of nine vulnerabilities known as "PwnedPiper" that left a widely-used pneumatic tube system (PTS) vulnerable to critical attacks, including a possibility of complete takeover. The security weaknesses, disclosed by American cybersecurity firm Armis, impact the Translogic PTS system by Swisslog Healthcare, which is installed in … [Read more...] about PwnedPiper PTS Security Flaws Threaten 80% of Hospitals in the U.S.
Why I Joined Cisco Security and Its Culture of Innovation and Inclusion
Perceptions, expectations, and reality Last month, I stepped into a new role as Senior Vice President and GM of Cloud and Network Security at Cisco Security Business Group. As with any new job, I am equal parts elated with the opportunity and submerged in learning about its Security portfolio and strategy. Now that I have some Cisco experience under my proverbial belt—albeit … [Read more...] about Why I Joined Cisco Security and Its Culture of Innovation and Inclusion
The Modern Security Operation Center
Every organization regardless of size, budget or area of focus should have some form of a security operation center (SOC). When I use the term “Security Operations Center”, many people imagine a dedicated team with expensive tools and a room full of monitors. That image can be a SOC, but it is not always the case. A SOC can just be one person or multiple groups of people spread … [Read more...] about The Modern Security Operation Center
A Visual Take on Email Authentication and Security
There is a saying that goes something like, "Do not judge a book by its cover." Yet, we all know we can not help but do just that - especially when it comes to online security. Logos play a significant role in whether or not we open an email and how we assess the importance of each message. Brand Indicators for Message Identification, or BIMI, aims to make it easier for us to … [Read more...] about A Visual Take on Email Authentication and Security
The Security Startup Ecosystem and the Trends Cisco is Watching
Building a company from the ground up is not for the faint of heart. I know, I’ve been there. As co-founder of Duo, the leading provider of Zero Trust access security, I know what it means to dedicate yourself fully to a vision, to your customers, and to your team. And I know how daunting it can be to find the right investors to join the team – people and organizations that … [Read more...] about The Security Startup Ecosystem and the Trends Cisco is Watching